The enterprise use of Third Party APIs (application programming interfaces) is exploding as businesses ramp up productivity and digital transformation. According to Research & Markets, the global API management market is expected to grow from USD 1.2 billion in 2018 to USD 5.1 billion by 2023, at a CAGR of 32.9% during the forecast period.
From integrating payments and digital marketing to mapping and push notifications, Third Party API usage is fast becoming a core dependency in many modern businesses. And the parallel rise in the number of disparate endpoints means this growth will not slow down.
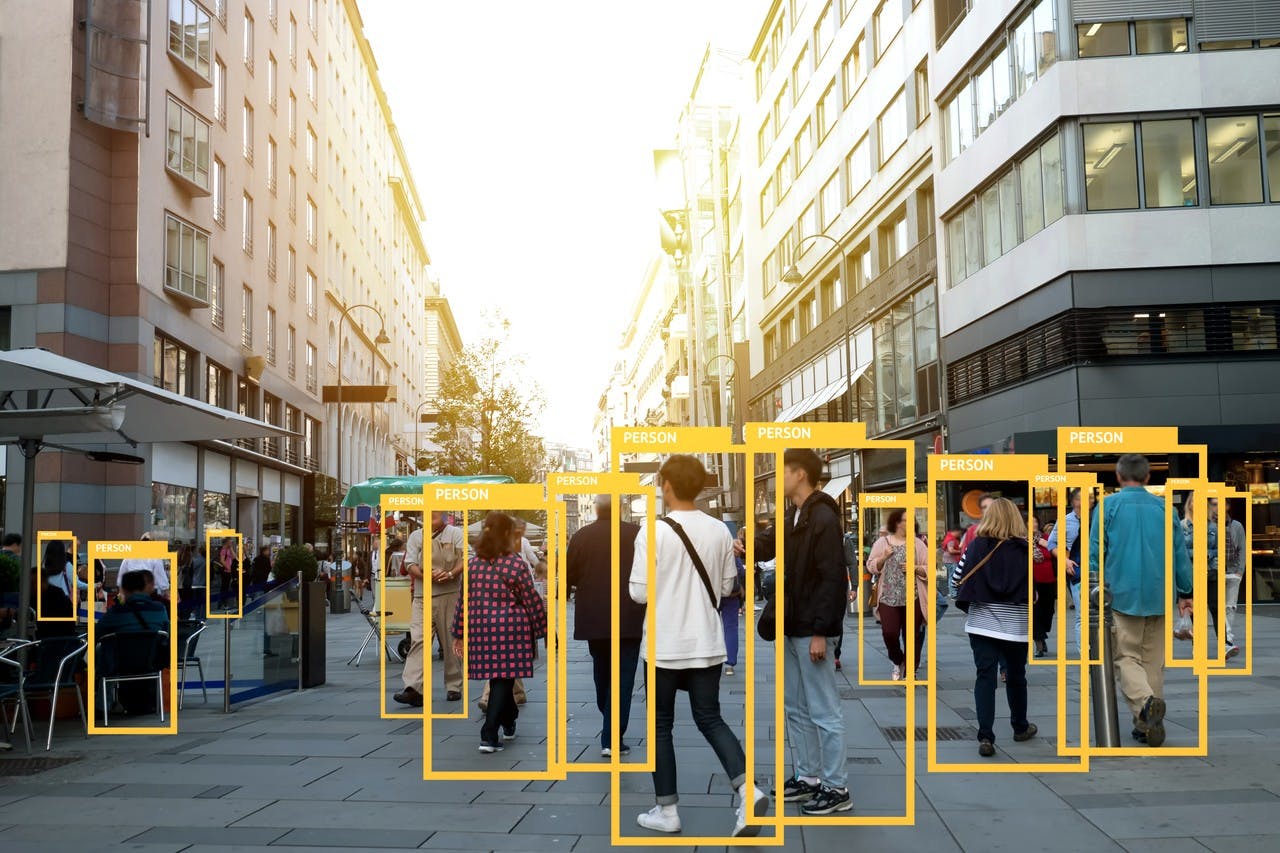
The threat is clear: Third Party API adoption is increasing the attack surface of our networks. What’s good for the developer is equally (if not more) good for the attacker, who now has multiple entry points to business critical data.
In September 2018, it was discovered that one of Facebook’s third party apps exposed over 1,000,000 records of Facebook user data. Essentially, the application was allowed to access user data through the Facebook API and copy all that information to an external server without strict protocols. Facebook isn’t the only major organization to suffer a data breach resulting from Third Party API infrastructure vulnerabilities. Many of the attacks actually go unreported — or worse — undetected.
Commonly, attackers take over accounts and steal photos and private information like credit card numbers and health records, all of which can be profitably sold on the Dark Web. The surge of IoT also means that infrastructure and devices are now more interconnected, making it possible for attackers to exploit vulnerabilities to cause physical harm.
A Booming API Security Market
The good news is that the number of vendors providing API security is also on the rise. Companies see the threats and the clear need to secure their API-related activities. According to Gartner, the market for API security product sales was worth USD 961 million in 2017 and is expected to grow at a CAGR of almost 15% from 2016 - 2021.
Many of the Third Party API security products today give the network administrator centralised control over the APIs for more efficient management.
“The lack of visibility of Third Party API infrastructure is a common pitfall for organizations. Getting that end-to-end visibility of access control permissions and software dependencies is a key step in helping developers identify their biggest risks so that they can implement systematic security policies.” said Horangi Chairman Kevin Lee.
Handling Third Party Risks
Organizations should ensure that all third-party apps employ proper protocols for secure communication between core business systems and the other applications. Google, for instance, defines stringent security and privacy policies for third party apps and extensions that need to access user data.
Developers can take advantage of self-learning code scanners like Horangi Scanner to scan the code base of the Third Party APIs and web applications for known vulnerabilities and help prevent insecure code from being published. Security tools that provide a granular view of traffic not just between Third Party APIs, but also between APIs, endpoints, and any data assets, will allow companies to quickly discover attackers, infrastructure breaches, and vulnerabilities.
While organizations are often faulted for being one step behind attackers, organizations can be proactive and make use of penetration testing for a thorough assessment of their security posture. Pentesting is not limited to third party applications and the codes behind them, but also applications, endpoints, servers, and security devices. Even if without an in-house expert, organizations today can choose to work with experienced security partners that provide such services.
Closing Thoughts
Third party applications might represent increased risk for the enterprise, but managed intelligently, organizations can continue to reap the productivity benefits of implementing Third Party APIs securely.