Category:
Cyber Threats
MOVEit Breach: The Largest Data Theft of 2023
This blog post dives into the MOVEit breach 2023, a significant cybersecurity incident impacting organizations and individuals globally. We explore the key factors contributing to the data breach, including the role of third-party risk management, incident response, and vulnerability and patch management, highlighting crucial lessons learned and strategies organizations can adopt to mitigate similar risks in the future.

What We Learned from the Biggest Data Breaches of 2022
Uber, Samsung, Twitter, Microsoft and more are among some of the biggest names affected in data breaches from last year. It goes to show that small or big, all organizations who use cyberinfrastructure can be at risk of a major security breach. Here are the key takeaways from the 10 biggest data breaches of 2022.

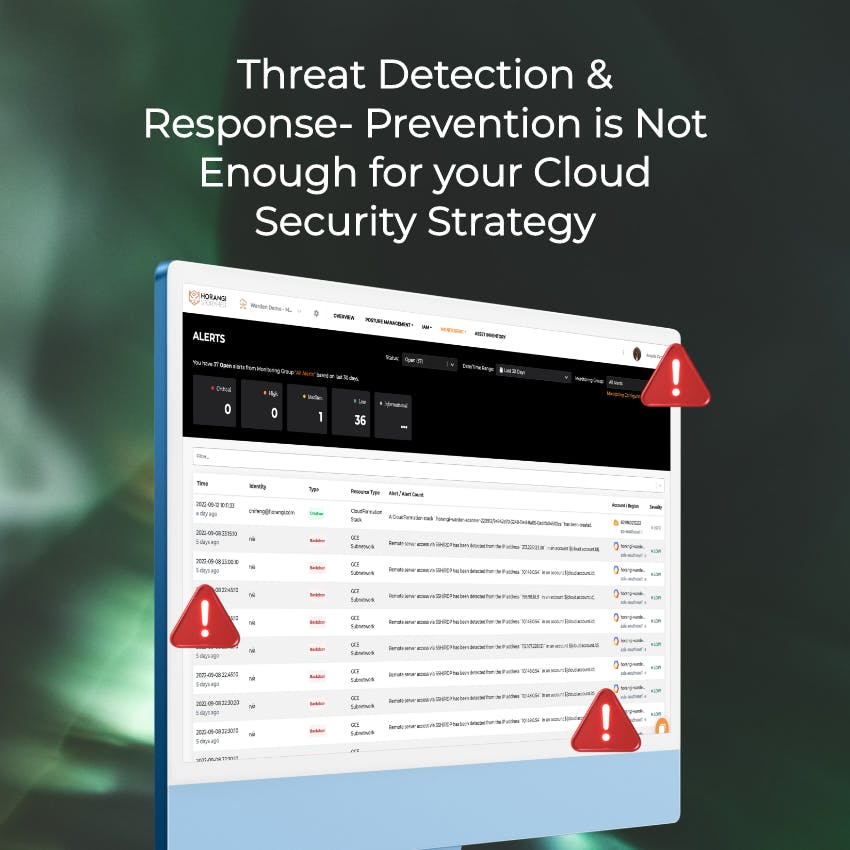
Threat Detection & Response: Prevention is Not Enough for your Cloud Security Strategy
It’s no secret that getting breached is a nightmare scenario, and it takes about 280 days for incident responders to detect and contain a breach, on average. Warden is enriched with intelligent threat detection for your multi-cloud environment, and continuously provides valuable detection use cases to enhance your company’s overall security posture.
Your browser's local storage can be misused. Here’s what you should know.
Are you aware that your favorite websites actually store information in your browser? Find out what information is stored and see how that can be misused in this blog.
4 Important Reasons Why Your Organization Needs Threat Detection
Many talk about the importance of complete threat prevention, but ultimately, there is always a need for threat detection in all areas of your organization, whether it is over your endpoints or IT infrastructure. Read this article to find out the top reasons why.

Killware: Malware That's Lethal
Ransomware incidents are headlining news and trade publications with increasing frequency so you’ll be familiar with it, but have you heard of killware?
Here's The Quick Fix For The Pwnkit Vulnerability (CVE-2021-4034) On Ubuntu
Don’t Be Pwned. Before hackers exploit it on your systems or a third party supplier’s system, learn more about the latest Pwnkit local privilege escalation vulnerability (CVE 2021-4034) and what you can do to remove it on Ubuntu.
Real Life Examples of Web Vulnerabilities (OWASP Top 10)
Knowing the common web vulnerabilities is great, but specific examples help demonstrate the relevance of these cybersecurity issues. Let’s take the approach of following the OWASP Top 10 list.
The Biggest Questions About Ransomware Answered
We go deep into what ransomware can and cannot do — jumping into misconceptions and myths about ransomware attacks and revealing the truth behind those notions.
How We Modified An Executable to Bypass Crowdstrike Falcon Endpoint Protection
Tasked to assess how an organization would stand up to ransomware attacks, Horangi looked to circumvent the defence mechanism of Crowdstrike Falcon, which was installed on the laptops of employees. This blog post documents the steps I took to complete this bypass.
2020 Cyber Attacks In Indonesia
In just 10 months, a whopping 324 million cyber attacks have been detected in Indonesia alone. This number has increased by nearly six-fold from the previous year. Here's a summary of what has happened and how your organization can take the cautionary steps to prevent such incidents.

Actionable Ransomware Defense The Horangi Way.
Understand the mechanics of different ransomware attacks from the MITRE ATT&CK Framework as we feature various scenarios to highlight defense opportunities you can leverage.
On-Demand Webinar: An Introduction to the MITRE ATT&CK Matrix
Want to understand the MITRE ATT&CK Matrix on a deeper level? Uncover common cyber attack patterns to shore up your organization's defenses with the expertise of Horangi Director of Cyber Operations Che Lin Law.
Teach A Man To Phish: Unpacking The Pyrogenic/Qealler Malware
From a trojan received in a phishing email, we break down how the malware is executed and what any organization can do to stay prepared for such security incidents.
Ransomware Attacks in 2020 [Infographic]
Ransomware continues to be a major threat in 2020. Here, we go through some of the high profile ransomware attacks in 2020 and implications to the businesses attacked.
Cybersecurity Labeling Scheme (CLS) in Singapore
The Cyber Security Agency in Singapore (CSA) is launching a Cybersecurity Labeling Scheme as part of its Safer Cyberspace Masterplan to better secure Singapore’s cyberspace and raise cyber hygiene levels.

The Cost of Cyber Attacks [Infographic]
A cyber attack compromises the security of a company’s cyber network and creates undesirable consequences for the business. We review the cost of a cyber attack to businesses, the key cyber attacks in 2019, and the importance of a well-fortified cybersecurity system.

Understanding Different Types of Ransomware
We explore the range of ransomware attacks and the basics your organization needs to know to stay prepared and minimize the damaging effects of ransomware.
Why Do Hackers Hack?
Get inside the mind of a hacker in this article as we explore what spurs hackers to do what they do. We learn about the abundant opportunities available for hacks today, including using hacking for good.

A Brief History of Ransomware
Ransomware is as commonplace in our lives today as email. All signs indicate that ransomware is not going away any time soon. So where did this nefarious family of malware come from?