What is Warden Threat Detection?
Warden Threat Detection monitors malicious activity and high-risk infrastructure changes in your cloud environments and sends real-time alerts when suspicious activity is detected.
- Alerts mapped to MITRE ATT3CK framework
- Detection of suspicious IPs
- High-risk infrastructure changes indicative of Defense Evasion, Persistence, Exfiltration, etc.
You can also manage Amazon GuardDuty findings and Warden threat detection alerts on a unified dashboard in Warden Monitoring. Read more below!
What is Amazon GuardDuty?
Amazon GuardDuty is a threat detection service that continuously monitors for malicious activity and unauthorized behavior to protect your Amazon Web Services accounts, workloads, and data stored in Amazon S3.
GuardDuty analyzes billions of events across your AWS accounts from AWS CloudTrail Management Events (AWS user and API activity in your accounts), AWS CloudTrail S3 Data Events (Amazon S3 activity), Amazon VPC Flow Logs (network traffic data), and DNS Logs (name query patterns).
Amazon GuardDuty threat detection identifies activity that can be associated with account compromise, instance compromise, malicious reconnaissance, and bucket compromise.
However, GuardDuty only supports threat detection on AWS cloud and the severity of the findings can be only defined by AWS, so as a user, you could not change it based on your team's need.
But with Warden Real-Time Threat Detection, you can use GuardDuty findings for your investigation and also fine-tune the rules configuration so that you efficiently manage and investigate alerts, based on your security needs.
Advantages of GuardDuty Integration with Warden Threat Detection
1. Fine-grained configuration to reduce noise
This integration will allow users to tune threat detection to have microscopic clarity, in tune with what their teams need and are able to handle. There are many different ways that you can set up configurations, such as:
- Flexible Grouping of Alerts: You can configure flexible grouping of alerts into logical groups that can match your organization’s needs. For example, you can set up a geographical focus where it alerts you for any suspicious activity from malicious locations. Also, instead of overwhelming multiple teams with alerts, you can direct these alerts towards a single team responsible for looking at these.
- Prioritize and Fix: You can also configure which rules you want to turn on and change the severity accordingly to meet each team’s security needs. This can help you to prioritize which alerts to address, while the security team focuses only on the alerts they care about the most.
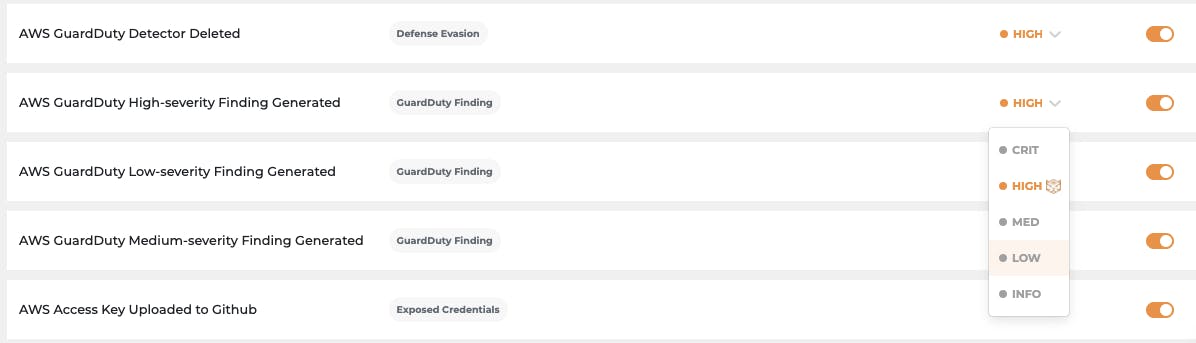
Prioritize and fix alerts based on your security team's needs
2. Speedy investigation to respond faster
Once you have set up the GuardDuty integration and start receiving alerts, investigation can also be done directly from the same monitoring page where you are triaging alerts. You can easily scan through all the events happening in your cloud environment including GuardDuty findings. Some events that you can track on-page are:
- Normalized events
- Quick filtering: IP, Users, Resources, Service events
- Raw logs
Conclusion
Consider implementing an all-in-one cloud security solution in your organization to make data analysis easier in threat detection and mitigation.
And if you are looking for a holistic cloud security solution like Warden equipped with real-time threat detection, CSPM, & CIEM capabilities, 300+ cloud security rules, and global compliance standards then get in touch with a Horangi Specialist for a quick demo of Warden, a comprehensive cloud security tool with IAM, Threat Detection, and Posture Management capabilities.