Enabling Microsoft Protected View
A new Zero-day attack on Microsoft Office affecting all current Office versions on all Windows operating systems was detected by Mcafee and FireEye on 7th April.
It is the latest in a long list of exploits; from the “Windows Word Intruder” kit that allowed beginners to create their own version of malware, to the phishing-led Cerber ransomware attack that millions of Microsoft 365 users were exposed to, Office is often targeted, commonly by social engineering with malicious files and macros.
This latest vulnerability has not been patched, and has been available for exploit since January 2017. It uses files with “.doc” extensions with a malicious OLE2link object embedded to download seemingly harmless HTML files, which hide .hta HTML Applications. The .hta file executes automatically to control the target machine, and hides itself behind a decoy document.
With this executable, attackers will be able to do code execution to perform actions of their choosing, bypassing the usual security controls.(https://securingtomorrow.mcafee.com/mcafee-labs/critical-office-zero-day-attacks-detected-wild/)
Fortunately, Microsoft Office has a built-in sandbox feature that allows you to preview files safely. Here are the steps to enable Microsoft Protected View, if it is not already enabled.
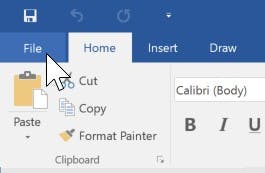
- Click on the “File” tab
- Open “Options” on the side bar
- Open “Trust Center”
- The options you want are under “Protected View”. It would also be a good idea to review your other security settings on the page.
This would also be a great opportunity to review other security settings, such as disabling Macros, ensuring older Office binary file types are disabled under “File Block Settings” and reviewing the list of trusted publishers and locations.
Lastly, remember to keep a lookout for suspicious attachments and files, and only open these files in a sandbox or a safe environment!