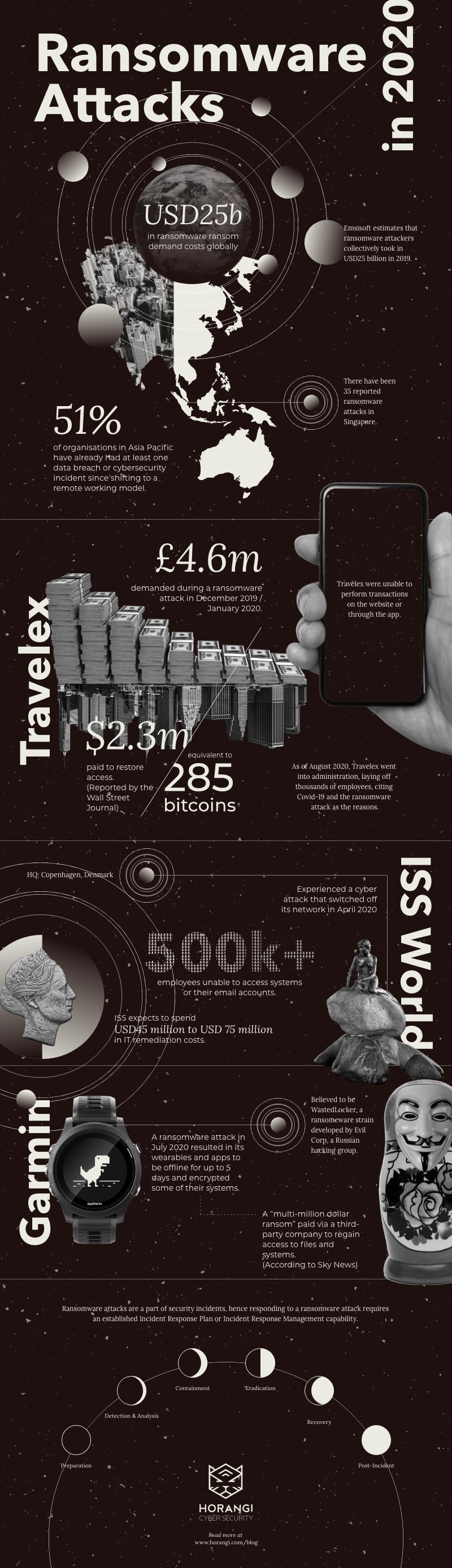
RansomwareRansomware continues to be a major threat in 2020 to organisations, and we are seeing a lot of household names getting attacked. Emsisoft estimates that ransomware attackers collectively took in USD25 billion in 2019. A Barracuda Networks report in 2020 indicated that 51% of organisations in Asia Pacific have already had at least one data breach or cybersecurity incident since shifting to a remote working model,
Perpetrators behind ransomware attacksPerpetrators behind ransomware attacks have done significant damage to critical infrastructures to household company names and collected billions of dollarscollected billions of dollars from their victims worldwide, and that is still going on today. What we have observed in the history of ransomwarethe history of ransomware is that hackers are moving on from individuals and home PC users to focus their time and energy on the big companies -- which usually translates to bigger ransom payments and bigger rewards, often in the millions of dollars. In Singapore alone, according to the Cyber Security Agency of Singapore, there were 35 reported cases of ransomware to SingCert in 2019, and these are just the reported cases!
Here we will go through the ransomware attacks in 2020, and what actions were taken by the victims.
Travelex - Ransomware attack
Foreign currency firm Travelex faced a ransomware attack in Dec 2019 / Jan 2020, rendering the company unable to perform financial transactions on the website or through the app.
Travelex was forced to take its websites offline during the busy holiday travelling season after discovering the ransomware attack and it was later discovered that the ransomware perpetrators responsible, Sodinokibi, had demanded £4.6m and was threatening to release Travelex’s customers’ personal data into the public domain.
In April 2020, it was reported that Travelex had paid the ransomware fee of $2.3 million (or about 285 bitcoins) to the hackers in order to restore their systems. What we do know is that the Travelex network is restored (potentially due to the payment), but the information regarding the customer data breach remains unknown.
Even more concerning for the business community is that Travelex went into administration in August 2020, laying off thousands of employees. Accounting firm PwC reports that this was due to a combination of COVID-19 and this recent ransomware attack, which shows all of us the real business cost of ransomware attacks.
ISS World - Cyber attack
In February 2020, ISS World, a facilities company headquartered in Copenhagen, faced a cyber attackcyber attack on its network and the attack managed to switch off its network, leaving its 500,000+ employee workforce without an ability to access their systems or email (report).
While ISS World did not confirm whether this was a ransomware attack, reports (including by BBC News) suggested that it is a ransomware attack.
By March 20, 2020, ISS World said it had regained control of most of its IT infrastructure and was systematically relaunching business-critical systems, albeit with somewhat reduced functionalities. ISS said it expects to be finished with restoring and rebuilding its systems and IT assets by the end of 2020.
In a company announcement, ISS expects to spend USD45 million to USD75 million on: remediating the IT incident; putting in workarounds to enable the continuous delivery of service, service underperformance because of system down-time, and cost duplication associated with contract operation. A rebuild of part of ISS’s IT infrastructure due to damage to some of the company’s IT assets is expected to cost between USD22.5 million and USD45 million.
Garmin - Ransomware attack
Fitness technology company Garmin was a victim of a cyber attack in July 2020 and resulted in its wearables, apps, website, as well as customer support functions to be offline for up to five days.
It is believed that the Garmin was hit by WastedLocker, a ransomware strain that some in the industry believe to be developed by Evil Corp, a Russian-based hacking group. In a statement, Garmin noted that the attack “encrypted some of our systems” in a statement.
According to Sky News, Garmin paid a “multi-million dollar ransom” via a third-party company to regain access to its files and systems.
In Asia Pacific: ST Engineering US subsidiary - Ransomware attack
Closer to Horangi’s HQ home in Singapore, Singapore-based ST Engineering Aerospace’s US subsidiary has suffered a ransomware attack in June 2020. Revealed by Cyfirma, this attack resulted in the exposure of confidential data which includes contract details with various governments, government-related organisations, and airlines.
VT San Antonio Aerospace, which provides aircraft services. acknowledged that the attack was carried out by the Maze (known in the industry as a sophisticated group of cyber criminals) and the perpetrators managed to gain unauthorized access to the network and launched their ransomware attack.
ST Engineering have noted that ST Engineering’s IT network in Singapore and its other businesses have not been compromised. Upon discovering the incident, ST Engineering reported that they have disconnected certain systems from the network, retaining leading third-party forensic advisors to help investigate the incident and notified law enforcement authorities.
Ok. I’ve been hit by ransomware. Now what?
Ransomware attacks are a part of security incidents, hence responding to a ransomware attack requires an established Incident Response Plan or Incident Response Management capability. The following are some actions that can be taken in the wake of a ransomware attack:
I. Preparation
- Impose human firewall by getting the best Incident Response Team to stop the ransomware at the early stage. This can also be achieved by providing specific training for the team.
- Establish an Incident Response Plan and Incident Response Team.
II. Detection and Analysis
- Analyze the situation through a tabletop exercise.
- Report suspicious behaviour.
- Use a sandbox that allows users to execute the suspected ransomware in a virtual system and analyze the behaviour of the ransomware.
III. Containment
- Reset authentication methods (passwords, entry codes and authentication keys.
- Sign out from all user accounts with administrative privileges.
- Isolate the infected systems and control the spread. Immediately disconnect these infected machines from the network.
- Block untrusted domains from the firewall.
- Report incidents to the regulatory body. The time required for reporting the incidents depends on applicable laws in each country. Failure to report before the deadline may cause the organization to incur severe penalties.
IV. Eradication
- Do not consider ransom payment as a first option. Find out if there are any ransomware decryption tools provided by select security agencies.
- Check the last backups. Confirm if they are valid and successfully completed.
V. Recovery
- Wipe the system and install the new OS.
VI. Follow Up / Post-incident
- Conduct a post-incident meeting to prevent the same attack from happening again.
- Update the material and document case in security awareness training materials.
- Send out a leadership message to all employees about learnings from the attack.