What’s New
- Quickly capture overall monitoring status with the alert summary
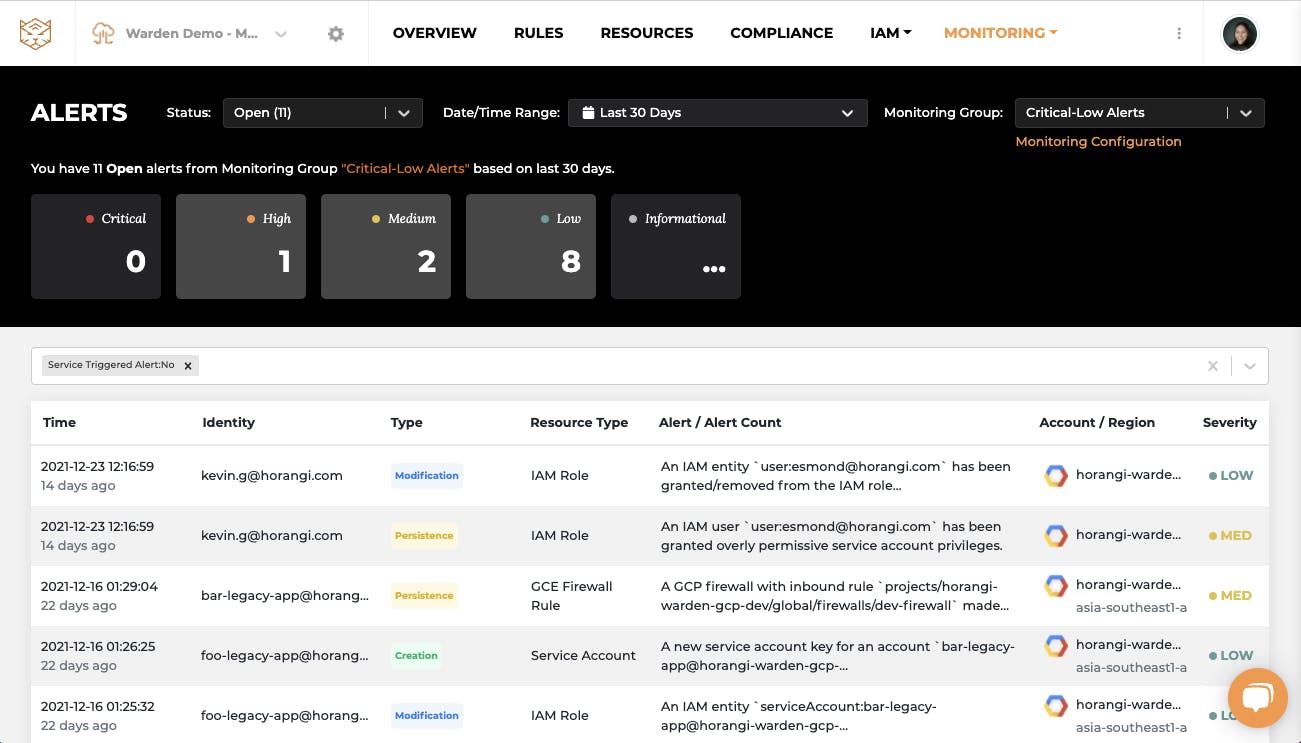
The new Monitoring alert page in Warden Threat Detection summarizes detected threats or anomalies by severity for all Monitoring Groups. These groups can be further prioritized based on personalized monitoring settings.
Monitoring alerts
- Quick access to monitoring configuration from the alerts page
If you want t o set up a new monitoring group or modify current monitoring scopes, now it’s just one click away.
Monitoring group
- Support simple workflow for alert triage
You can now also get notified for Status changes for discovered alerts that need attention. This can significantly reduce mean-time to respond as you focus on new threats or anomalies marked as ‘open status’ (default setting). You can snooze other alerts after triage by changing the alert status so there’s no alert fatigue.
Change alert status
How it helps you and your organization
These feature add-ons on Warden Threat Detection can help you flag anomalous behaviours such as when someone accesses your infrastructure from an unusual geolocation or using malicious user agents or IPs, or if someone is provisioning a high number of compute instances or high-risk infrastructure changes such as turning off logging or mass deletion of resources.
If such incidents happen, you will get real-time alerts via messaging platforms like Slack or you can check the alerts summarized for you on the brand new monitoring alert page. It gives you a clear understanding of prioritized threats or anomalies that happened during the selected period of time. It also quickly drills them down to more specific types of alerts for details or can be optimized to only focus on critical alerts.
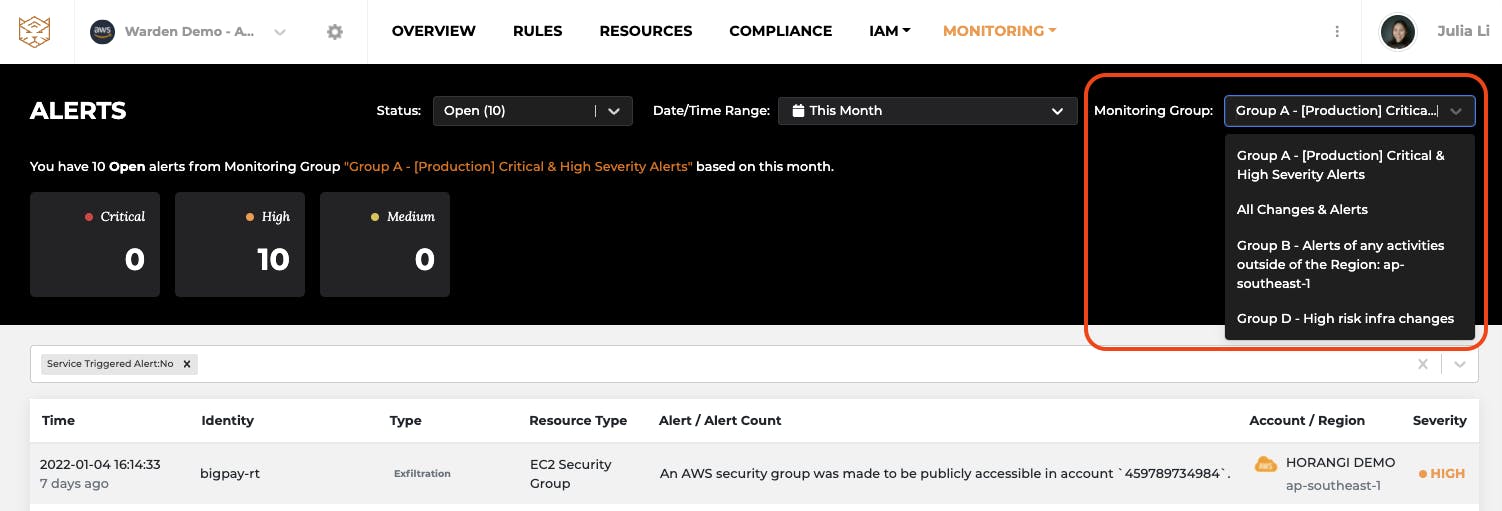
What is even better is all the detection could be tuned based on your monitoring needs and the default summary view would be customized for you upon setup. You can limit the scope being monitored to a specific account, cloud provider or region, or exclude specific trusted users from the monitoring group, then all the activities from whitelisted users will be suppressed by default and alerts will only be triggered to flag suspicious conditions.
For example, you are an engineering Lead and want to only monitor important infrastructure changes such as changes in the production environment, activities outside of your region or excluding CI/CD users. Then these features on Warden can be extremely helpful for you. These features also help you utilize your incident response process with Warden Threat Detection.
Once your investigation is done, you can change the alert status to ‘Suppressed’ if it is a false positive, or to ‘Resolved’ if you are done with the response. You also can mark the status as ‘Acknowledged’ so that other team members can know that it is being investigated. After you clear out the alerts, you will always see ‘NO NEW THREATS’ sign until new threats or anomalies are detected, which shows your cloud infrastructure is secured and protected.
More information about setting up the monitoring group can be found here.
Conclusion
We have often heard from our customers that it can be quite time-consuming to investigate alerts and resolve them in-time. With these feature updates, we hope to help you automate investigation and significantly reduce your time to respond to threats lurking in your cloud stack. All of the processes, features enhancements, and add-ons are designed to accelerate your security team’s ease-of-use and to minimize the time spent on investigation. Warden will continue to add more features for faster and efficient investigation. To know more or experience Warden’s Intelligent Threat Detection in a 15-min demo, drop us a line here.




