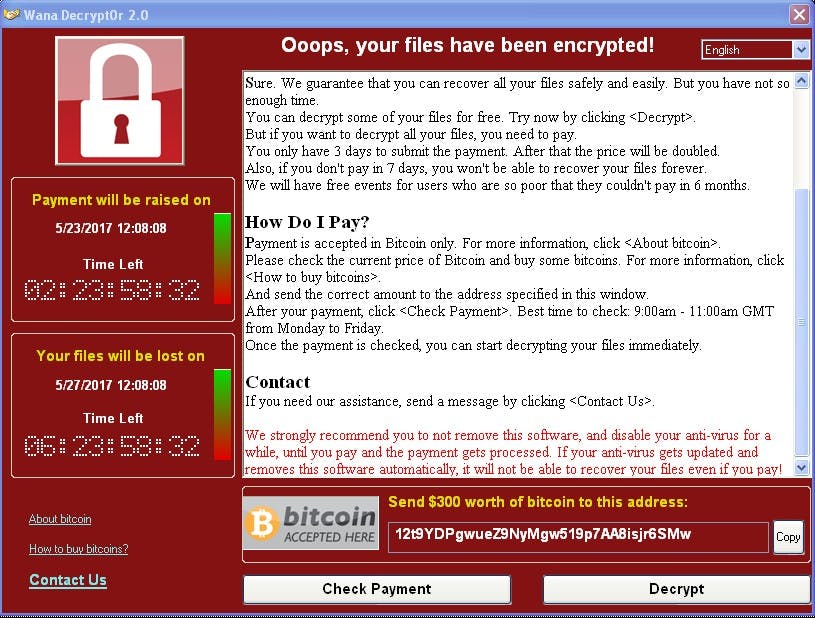
What is WanaCrypt0r anyway?
WanaCrypt0r or Wcry is the malware behind the WannaCry ransomware campaign. The campaign was launched on Friday, May 12, 2017 and quickly affected victims all over the world, including high-profile organizations such as England’s National Health Service and Telephonica, a Spanish telecom firm.
Was anyone targeted?
No, the WannaCry campaign does not appear to target specific countries, organizations, or people. In fact it appears to have a broad scope that impacts organizations in 150 countries and across all industries. From a technical perspective, the ransomware will exploit Windows systems vulnerable to CVE-2017–0144 which impacts the SMB service. It would be a fair statement to say that systems with this vulnerability are targeted, likely without consideration of other geographical, business, or political factors.
Why is it such a big deal?
WanaCrypt0r scans the network and internet for systems with port 445 associated with SMB and identifies those vulnerable to CVE-2017–0144. This exploit was made famous by the Shadow Brokers after their fifth leak where exploits believed to be used by NSA were made public.
In addition, the ability to scan, identify a vulnerability, and automatically infect a system means the malware is capable of propagating on its own without human interaction. Self replicating malware is much more dangerous, due to its ability to infect portions of an organization that don’t regularly get infected with malware, such as MRI machines and other medical devices.
The global spread of WanaCrypt0r and the nature of the high-profile victims have shed light on the high risk and potential for high impact of malware-based attacks.
How does my organization get infected?
First, we know that WanaCrypt0r will scan the network for CVE-2017–0144and will automatically spread from there. So the real question is “how do the very first systems get infected?”
There are multiple theories on how WanaCrypt0r makes its way into an environment:
- Phishing emails
- Exploitable remote access applications
- SMB available to the internet
- Existing malware or botnet infections
While we do see a large number of phishing emails and exploitable remote access applications during investigations, our experience is that the strategy for deploying malware that can self-replicate doesn’t frequently involve these infiltration vectors. Instead, the strategy we see used in these scenarios is the attacker targeting a large number of systems they know are vulnerable while using as little human interaction as possible. Normally this means that they will utilize an existing botnet to infect its set of hosts or they will scan the internet for available targets.
The best strategy is to secure an organization against all of these vectors.
How do I protect my organization from WanaCrypt0r?
The short answer is easy, good security hygiene! The long answer is a bit more complicated.
Specifically for WanaCrypt0r, it’s important to make sure that MS17–010 is patched on all systems:
https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
It’s important to note that patching alone might not prevent future ransomware attacks, and might not even protect against the next version of WanaCrypt0r. Preventing a wide-spread ransomwareransomware infection, such as WanaCrypt0r, requires a few steps with overlapping security strategies:
- Deploy an effective patch management program.
- Segment the network.
- Regularly complete goal-based security assessments.
Patch management programs are notoriously difficult to deploy, especially when they require maintenance on systems with components that are no longer supported by their creators. This makes patch management, by itself, an ineffective prevention strategy. Instead, an organization should compensate by also using network segmentation and goal-based assessments.
Installing patches is kind of like locking the doors; if an attacker really wants to get in they can just walk around the house until they find the hide-a-key or wait for other doors to open. It’s really just a matter of time before they get in.
Network segmentation is akin to closing the motorway that leads to a home, the attacker can’t get close enough to even know how many doors the house has. This is definitely more effective but a dedicated criminal might find another way to drive or even get out of his car and walk to the door.
Goal-based security assessments are similar to police patrolling a neighborhood.
Policemen seek out alternate routes that criminals might utilize to get to the house when the motorway is closed. Good policemen will also get to know the citizens and businesses in their zone; they might even offer advice on better methods for securing against intruders and preventing future crime. They are also are equipped to easily detect something unusual, such as an open back door in the middle of the night or a suspicious person loitering in the car park. When they do find something wrong, they have a highly effective triage system for responding with the correct amount of resources. When looking to accomplish a complex mission, too few officers will be unsuccessful and too many is unsustainable. Instead an appropriate response with professionals will get the job done correctly.
The same is true of goal based security assessments; they might not always prevent an attack but security posture will continue to get better over time. When something bad happens, the response will be swift and the impact will be lower.