The State of Cybersecurity in Singapore is ever-changing and in a positive way, so many things have changed since I moved here in 2013. It’s been exciting to have seen and been part of this rapidly-developing tech ecosystem over the past 7 years, from the new companies to innovations. When I first arrived from Korea in 2013, the tech scene was still fairly small and venture capital firms had just started coming in. The next few years saw massive growth jointly created by government support, the rise in venture capital interest and investment, and the entry of Cloud Service Providers (CSP) including Amazon Web Services (AWS), Google Cloud Platform (GCP), and Microsoft Azure. The proliferation of the cloud certainly made the environment ripe to grow and made it much easier to build tech companies.
The Government’s Cybersecurity Initiatives
At the same time, the Singapore government has been working to improve cybersecurity awarenessimprove cybersecurity awareness, infrastructure, and investment into the ecosystem over the past 10 years. This has been an important part of Singapore’s progress as a whole as well as making it the Southeast Asia tech hub that it is.
Singapore has announced quite a few updates including the Cyber Security Agency of Singapore’s (CSA) Cybersecurity Act, Cybersecurity Labelling Scheme (CLS)Cybersecurity Labelling Scheme (CLS) as part of Singapore's Safer Cyberspace Masterplan, as well as the Singapore Cyber Landscape.
A summary of these schemes and regulations as follows:
Cybersecurity Act
Released in February of 2018 to help do 4 things in Singapore:
- Strengthen the protection of Critical Information Infrastructure (CII) against cyber attacks.
- Authorize CSA to prevent and respond to cybersecurity threats and incidents.
- Establish a framework for sharing cybersecurity information.
- Establish a light-touch licensing framework for cybersecurity service providers.
Singapore’s Operational Technology Cybersecurity Masterplan 2019
Designed to enhance the security of Singapore’s critical sectors to improve cross-sector response and strengthen partnerships with industry.
Singapore Cyber Landscape
An informational and easy-to-read annual report to understand what type of attacks and cybersecurity issues are being faced in Singapore, to see what is actually happening on the ground.
Cybersecurity Labeling Scheme (CLS)
The CLS aims to incentivize manufacturers to develop and provide products with better cybersecurity features. The cybersecurity labels will also serve to differentiate smart devices with better cybersecurity provisions in the market, from their competitors.
Emerging Security Challenges Facing Singapore Organizations
Cloud Adoption Risks
A majority of the tech companies in Singapore are now utilizing the benefits of the cloud, but more recently a lot of the traditional SMEs are making the switch as well. While there are clear advantages in making this switch there are also challenges.
Training a traditional IT team to make the switch to the cloud is not an easy task. Managing security and complianceManaging security and compliance in the cloud requires different skill sets from those in a traditional IT environment. Plus, cloud technologies are still evolving and, if left unchecked, could very quickly breed a shadow IT environment. What this means is that organizations must have visibility of their cloud software and resources. On public cloud Infrastructure-as-a-Service (IaaS) usage alone, Horangi’s cloud security software WardenHorangi’s cloud security software Warden has found that 99% of cloud environments it has scanned have exposed security vulnerabilities that could have led to data breaches.
Remote Work Extended
While none of us could have predicted the impact that COVID-19 would have on both the economy and work cadence, it has likely changed the way organizations work for the foreseeable future, not just in Singapore.
The traditional security strategy of perimeter defense around corporate networks can no longer be depended on in this new normal. From unsecured routers and bigger risks of Business Email Compromise (BEC) to increased adoption of cloud-based productivity software, security teams have to implement new policies that both enable and secure their remote workforce.
Lack of Cybersecurity Awareness & Professionals
The CSA reported last month that there were three times more phishing attacks in Singapore in 2019 and twice as many during the COVID-19 pandemic. With the news of the various government-funded support initiatives in Singapore, CYFIRMA also got wind of a massive phishing campaign targeting Singapore entities. That only goes to show that a significant portion of cyber attacks in this region involve some element of phishing. And it is the lack of cybersecurity awareness that makes phishing attacks still so effective today.
The problem is exacerbated because of the shortage of security professionals in the region. As seen from the graph below, in Southeast Asia alone, only 10% of organizations have a CISO. And for companies that have CISOs, these leaders struggle to find talent for their teams, as (ISC)² revealed in a 2018 report that the shortage of skilled cybersecurity professionals is a major challenge, with the APAC region experiencing the highest shortage at around 2.15 million.
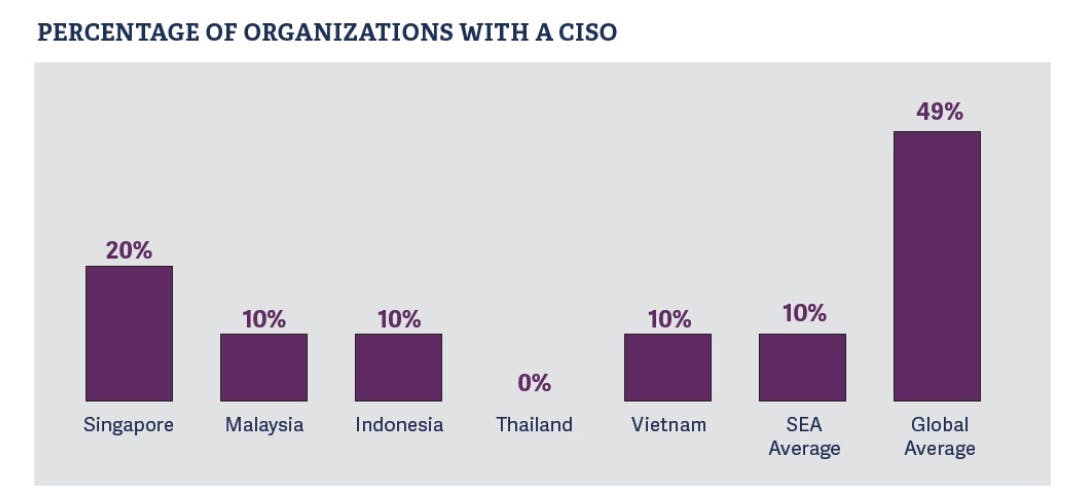
Graph taken from Russell Reynolds Associates: Technology Talent Talk: Foundational Technology Officers in Southeast Asia
How To Address The Risks
Build A Security Culture
Instilling cybersecurity into company culture is free and also the biggest bang for your buck at a company of any size. If the employees know that the C-levels care about security and it is talked about regularly enough, the security posture of the company will get stronger. Also, take some time every day to learn about what hackers are doing today. How are scams being conducted? Education is free and helping yourself and your colleaguesEducation is free and helping yourself and your colleagues be aware will lower human vulnerability significantly.
Understand Cybersecurity Frameworks To Benchmark Best Practices
NIST and SOC 2 are examples of cybersecurity frameworkscybersecurity frameworks that can act as benchmarks for your organization’s security best practices. Identify which frameworks and compliance standards are relevant to your organization so you can work towards them.
Do A Gap Assessment
If you have the budget, doing a Cybersecurity AssessmentCybersecurity Assessment allows your organization to understand your strengths and weaknesses against your relevant compliance standards. At the end of the day, cybersecurity is a people problem, and understanding your gaps will facilitate the creation of a long-term security strategy and roadmap that prioritizes what your people should do in building a strong security posture.
In The Cloud Or Soon To Be? Get A Security & Compliance Solution
Solutions like Horangi’s Warden (a Cloud Security Posture ManagementCloud Security Posture Management solution) help organizations to automate security and compliance. Since not every organization will be staffed with cloud securitycloud security experts, adopting such easy-to-use solutions can allow you to have an acceptable baseline for security and even demonstrate to auditors that you are compliant with recognized security frameworks.




