The meeting between United States President Donald Trump with North Korean Leader Kim Jong Un during the June 12 summit in the garden city of Singapore was a historic moment in the field of international relations. Despite the eyes of the world being glued to this key positive checkpoint in the US-DPRK relationship, the media was spinning up another story with more sinister undertones.
What’s in the bag!?
As part of welfare packages provided to various media crews covering the event was a small fan that can be powered through the USB port of a smartphone. Provided to combat the heat of Singapore’s tropical climate. However the high-profile and political nature of the summit lead a Dutch journalist in Singapore to suggest that the small USB-Fan, whose production origin remains unclear, can be easily exploited as a surveillance device to support international cyber-espionage objectives.
Making references to former cases where state intelligence agencies modified various electronic devices to support signals intelligence (SIGINT) objectives, the accusation exploded across the Twitterverse and drew the attention of spyware geeks, techies and security specialists - such as ourselves at Horangi. Soon, tweets started surfacing with “security experts” advising the media not to plug the fan into their device fearing that it might be a Trojan/Malware or even a surveillance device.
Determining The Plausibility
Singaporean government agencies were quick to respond to clarify that “the USB fans are simple devices with no storage or processing capabilities”. However, the entire spyware concern got us thinking… i) How did the journalists and other ‘experts’ arrive at the conclusion that it is a malicious device beyond being just a fan? ii) Could we verify response from the authorities about the fan’s inability to possess data storage and processing capabilities? And iii) What are the operational and tactical aspects of such a device if it really existed? With those burning questions in mind, our own cyber operations consultant, Johnson Thiang, decided to tear the device apart to discover the truth behind this mysterious fan!
STEP 1: GET THE FAN!

Thanks to our contacts in the media industry, we were able to obtain a brand-new and sealed fan from the welfare kit provided to journalists covering the summit. Now, we can proceed to perform a teardown of the device to find out if it is more than just a fan.
STEP 2: TEAR IT APART!

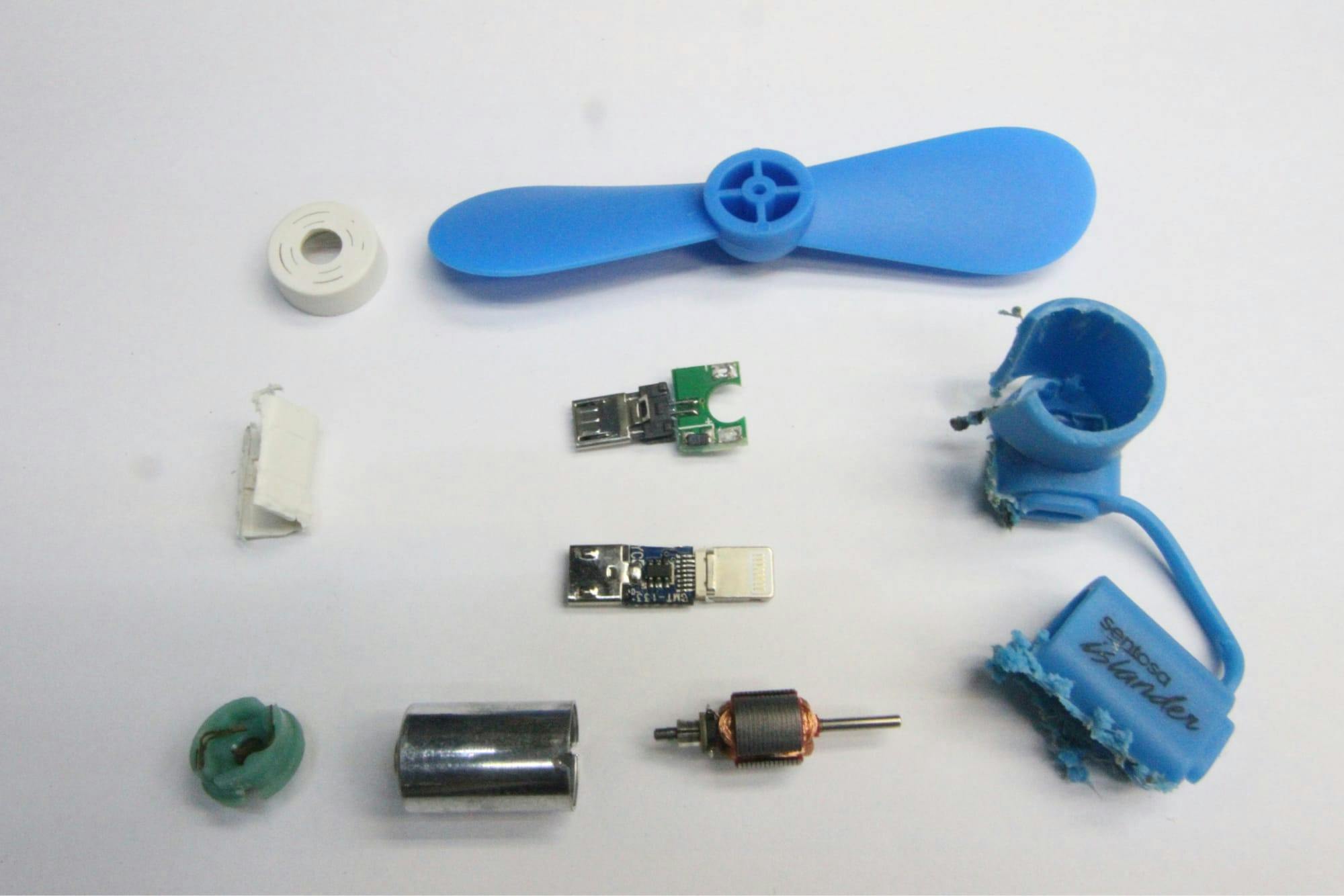
The package is made up of 3 removable parts, a fan blade (Top left), the motor and micro-USB to lightning adapter (Middle right) and a front cover for the motor. (Bottom) The fan’s blade and the front motor cover are just plastic pieces with no functionality so let’s just focus on the main fan motor and adapter.
STEP 3: GETTING SURGICAL!

There seem to be no obvious entry point in to the device itself so let’s break out the power tools. Gutting the various components of the fan and one-minute later we have it naked, in all its glory.
STEP 4: WHAT’S INSIDE?
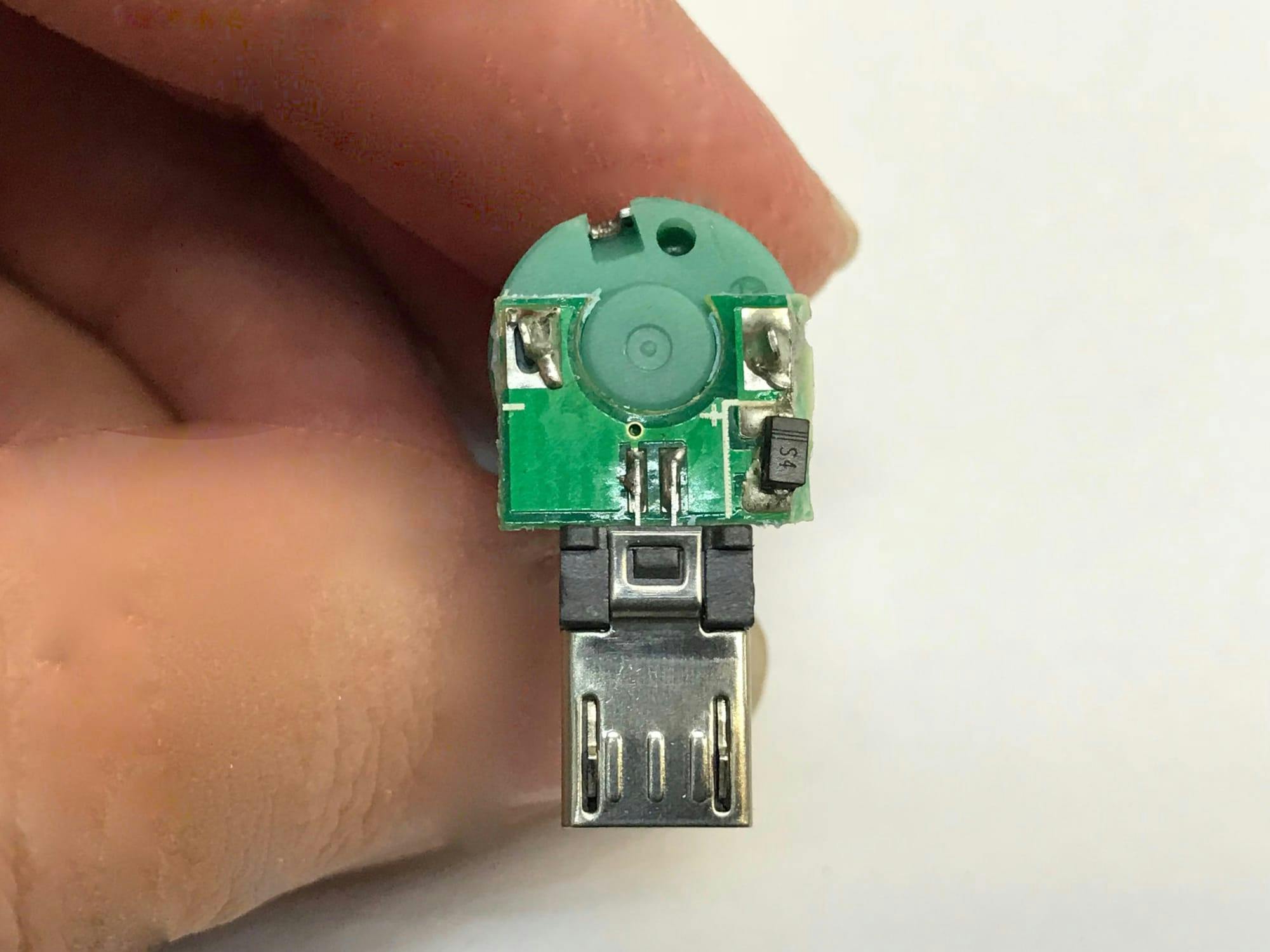

The fan has a simple electrical construction of a motor, a printed circuit board and a connector. Flipping it over will give us a good view of what’s on the circuit board. A very simple board with only 1 component and a connector. Ah that black thing at the bottom right of the circuit board! Is it a spy chip? Let’s zoom in and take a closer look.
It has 3 strokes and S4 labelled on the chip. A quick search on google says that it is a surface mounted schottky barrier diode. So nope, it is not a spy chip. It is to prevent reverse voltage from the motor from damaging the power source, i.e your phone. How about the other part, the motor? Sure, teardown it is.
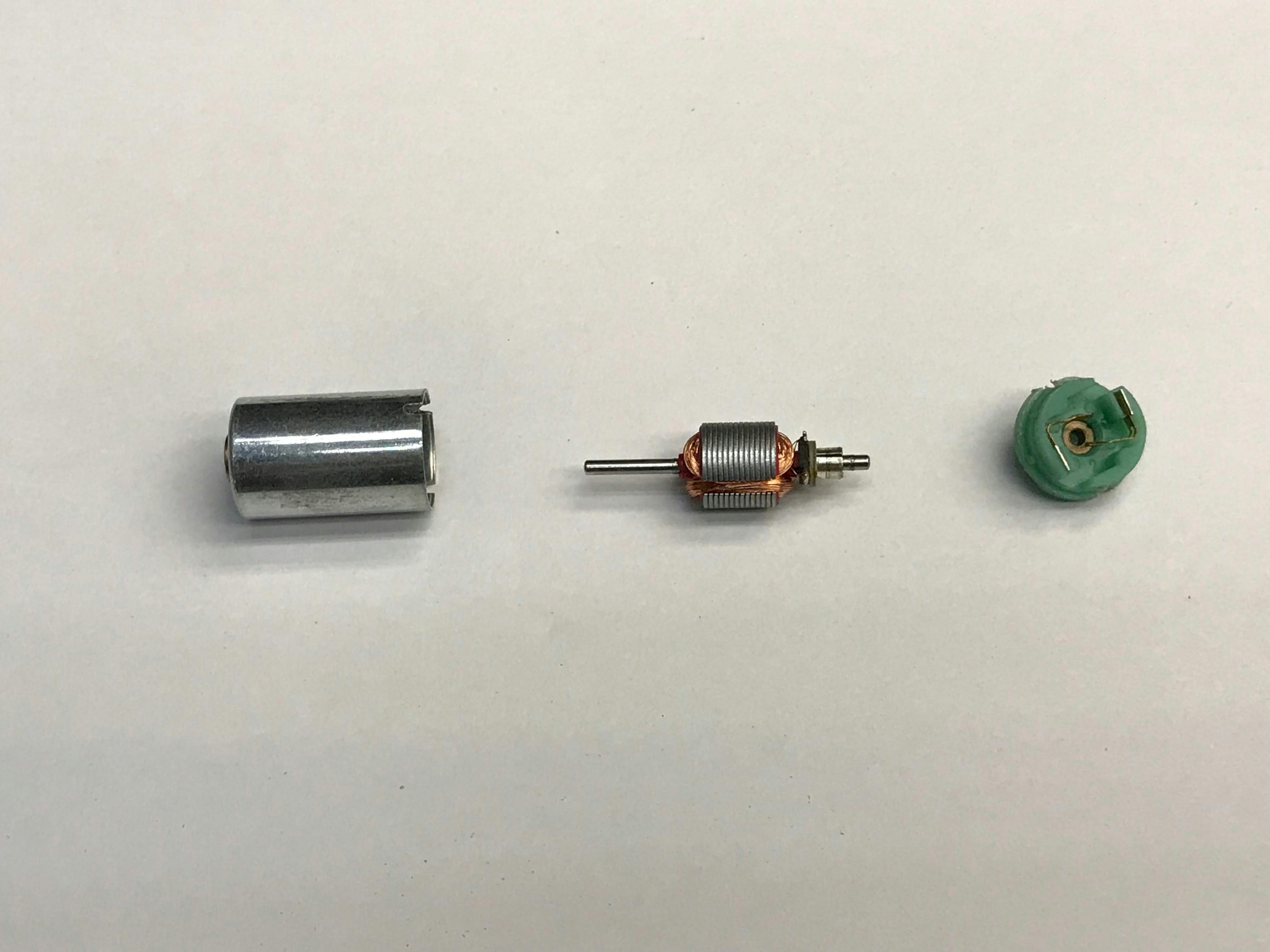
Magnets checked, rotor with windings checked, motor case with brushes checked. Spy device, nope.

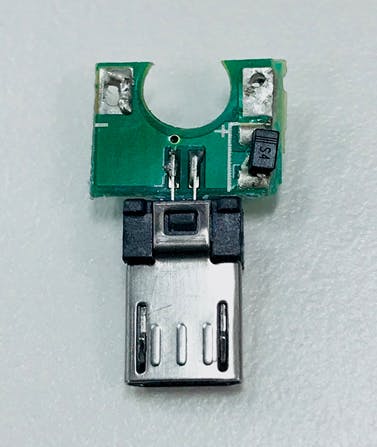
But wait a minute, how about the converter from micro USB to lightning connector?

The back of the converter has 4 components, 1 male lightning connector, 1 female micro-usb connector and 2 SMD capacitors. Simple electrical components, nothing fancy. How about the front?
STEP 5: ZOOMING IN.
Trust me, with limited lighting it was really hard to capture the information on the chip. Nevertheless, we got it and… we have no idea what is that chip. No amount of googling turned up reliable results. But what we do know is that, for any accessory to work with an iPhone, it requires an authentication chip in the lightning connector. The official cable contains an EEPROM to tell the phone that it is a legit cable. This chip is probably a micro-controller to emulate the function so that the fan can draw power from the lightning port. There is this article that talks about other non MFi certified components look like and one of them look very similar to the converter that we have.
Technically and Operationally Plausible?
The answer here, specific to the USB-Fan from the media welfare packages, is not plausible. From a technical perspective, the fan simply did not possess the necessary equipment to be a functional surveillance device as it lacks any indication of possessing reception, transmission, or storage capabilities. Aside from the unknown chip, the USB-Fan was simply not designed to hold more components (i.e. processor, transmitter, microphone, or storage disk) required of a functional surveillance bug. The USB-Fan devices did not possess any means of data storage or process as identified earlier.
Such a device would also not work from an operational perspective to support intelligence objectives. Should the fan itself be a surveillance bug, it would pick up too much audio and signals interference. First, the device was designed to be used outdoors and will also be picking up much of the surrounding environment (i.e. Camera Shutters). Second, the motor would also produce a magnetic field that might disrupt any transmitter or receiving unit embedded within. Such diplomatic summits, whilst highly televised, is also highly sensitive. Media staff is usually provided access to various periods of the summit but often denied access to real diplomatic discussions that happen behind closed doors. Therefore, it holds no intelligence value in targeting media staff to support surveillance, or bugging, means. However, what intelligence objectives can be achieved within the context of this scenario?
We raise this question to our own intelligence expert, Cheng Lai Ki, a former military commander holding a Master’s degree in Intelligence and International Security from the War Studies Department at King’s College London in the United Kingdom.
Propaganda Through Social Engineering
The most likely answer is propaganda control through social engineering, where the device facilitates a follow-on operation of manipulating the information produced by the media outlets. Articles discussing the USB-Fan, like the one on Yahoo News that was published on 12 June made constant references to USB devices used in other espionage cases involving state intelligence services such as the Russian Foreign Intelligence Service (KGB). These devices were essentially all mass-storage devices luring victims through social engineering efforts. However, within the current scenario the fan would need to have an additional phase to support its value as an intelligence asset.
The fan is the preverbal Trojan Horse, luring users to download an accompanying Third-Party Application into their connected smartphones. Agencies only have to bypass the initial download, which is often protected by security features on the Apple and GooglePlay stores, and can be easily accomplished through manipulating a systems update.
The intelligence target here is neither the smartphone nor the summit, but more the information produced by the media staff. To former communist countries such as North Korea, Russia and China, authoritarian control over the media is nothing new. For example, the Chinese government keeps a very tight reign over its media censorship to preserve the image of the nation to the outside world as well as preventing 'toxic' material from influencing its citizens. If anything, an intelligence operation against the media would more likely involve propaganda control by monitoring the content released about the North Korean President or the summit itself. This can also be a means to support threatening actions such as Distributed Denial of Service (DDoS) and ransomware attacks against ‘non compliant’ media outlets.
Diagnosis: An Orwellian Scare
The original accusations are simply not technologically or operationally plausible and attributed to an orwellian scare of a big brother government monitoring our every move. We live in a world where technologies are advancing rapidly, and bringing to life many tools that were once thought to be fictional features in various blockbuster films.
Majority of society is consistently carrying pocket sized computers with all the tools intelligence agencies would require to support espionage operations. Whilst it is not impossible that such surveillance solutions are not being implemented by national intelligence agencies such as the Israeli Mossad or the DPRK Bureau 121, it is important to understand how technologies today have revolutionized conventional intelligence operations; before initiating accusations of espionage.
Conclusion: Verify Your News & Remain Cautious
It is imperative to verify the opinions that hurl accusations of espionage, whilst also being cautious of items given freely to you in an attempt at social engineering. In a world of rapid technological advancement and instant news it is difficult verify what is true and what has changed. We hope you liked our fun but critical exercise to determine whether the ‘Fan’ was an object of suspicion. We also hope our article furnishes you a new and fresh perspective to critically evaluate the landscape about you.



