In this February release, the Warden team worked on adding General Data Protection Regulations (GDPR) as a compliance standard. With control items fully mapped to Warden rules, our customers can look forward to more comprehensive compliance coverage across all areas of operation. Some highlights of this compliance mapping include clauses 25, 30, and 32 inside the GDPR.
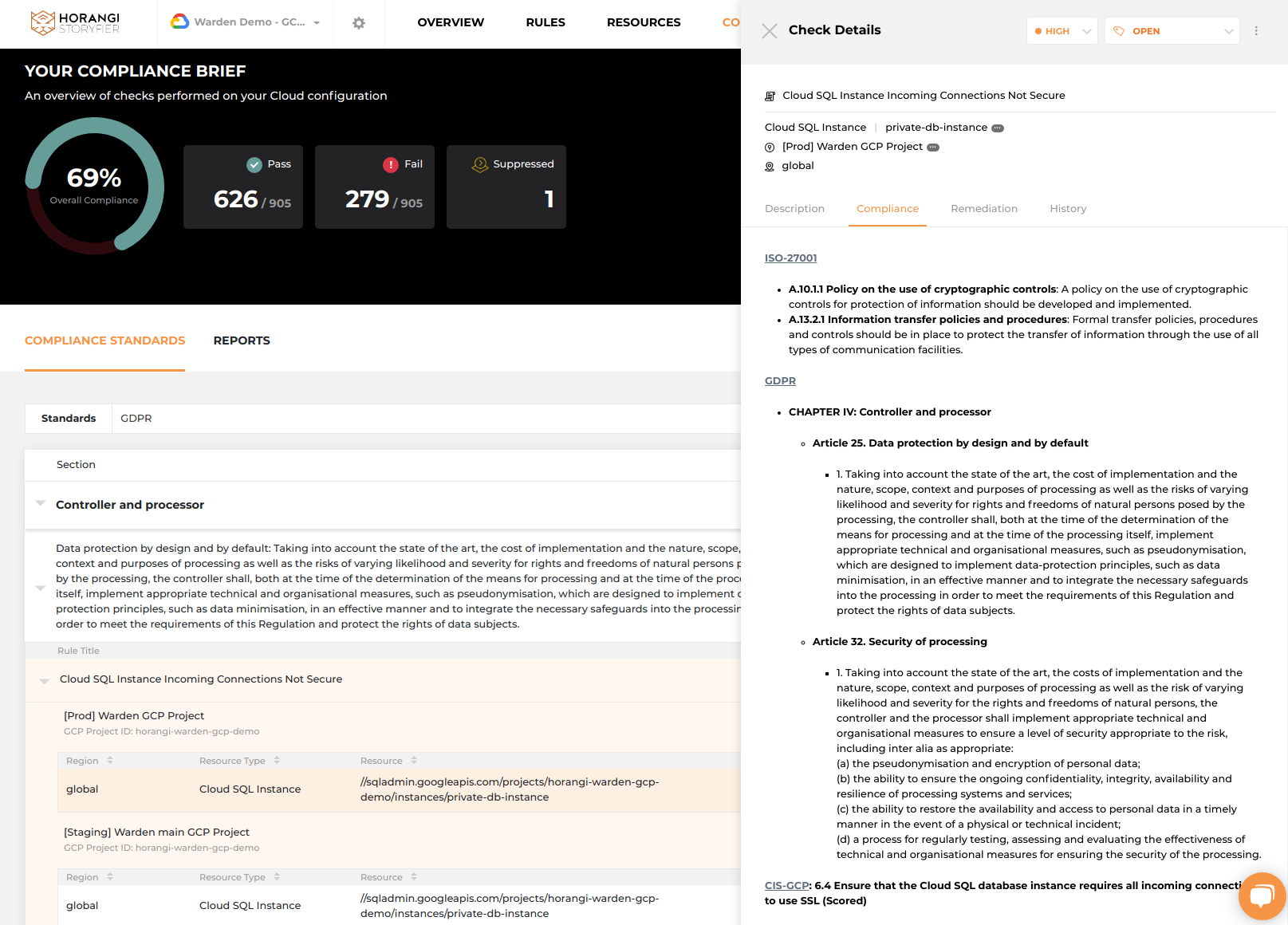
Clause 32(1): On implementing appropriate technical and organizational measures to ensure a level of security appropriate to the risk, including inter alia as appropriate
Mapped rules include:
- RDS Instance Encryption Not Enabled
- S3 Bucket Default Server-Side Encryption Not Enabled
- AWS S3 Bucket with Public Read Permission
- AWS S3 Bucket with Public Write Permission
- Compute Persistent Disk Not Encrypted With CSEK
Clause 32(2): On assessing security levels in relation to accidental or unlawful destruction, loss, alteration, or unauthorized disclosure or access of personal data
Mapped rules include:
- IAM User MFA Not Enabled
- VPC Endpoints Exposed
- BigQuery Datasets Publicly Accessible
What This Means
- Warden itself is a means to support clause 32(1)(d): a process for regularly testing, assessing and evaluating the effectiveness of technical and organizational measures for ensuring the security of the processing.
- Warden is able to automatically check for encryption of personal data, as stated in clause 32(1)(a)
- Confidentiality and prevention of unauthorized access is supported by Warden IAM and network security rules, highlighted in clause 32(1)(b) and 32(2)
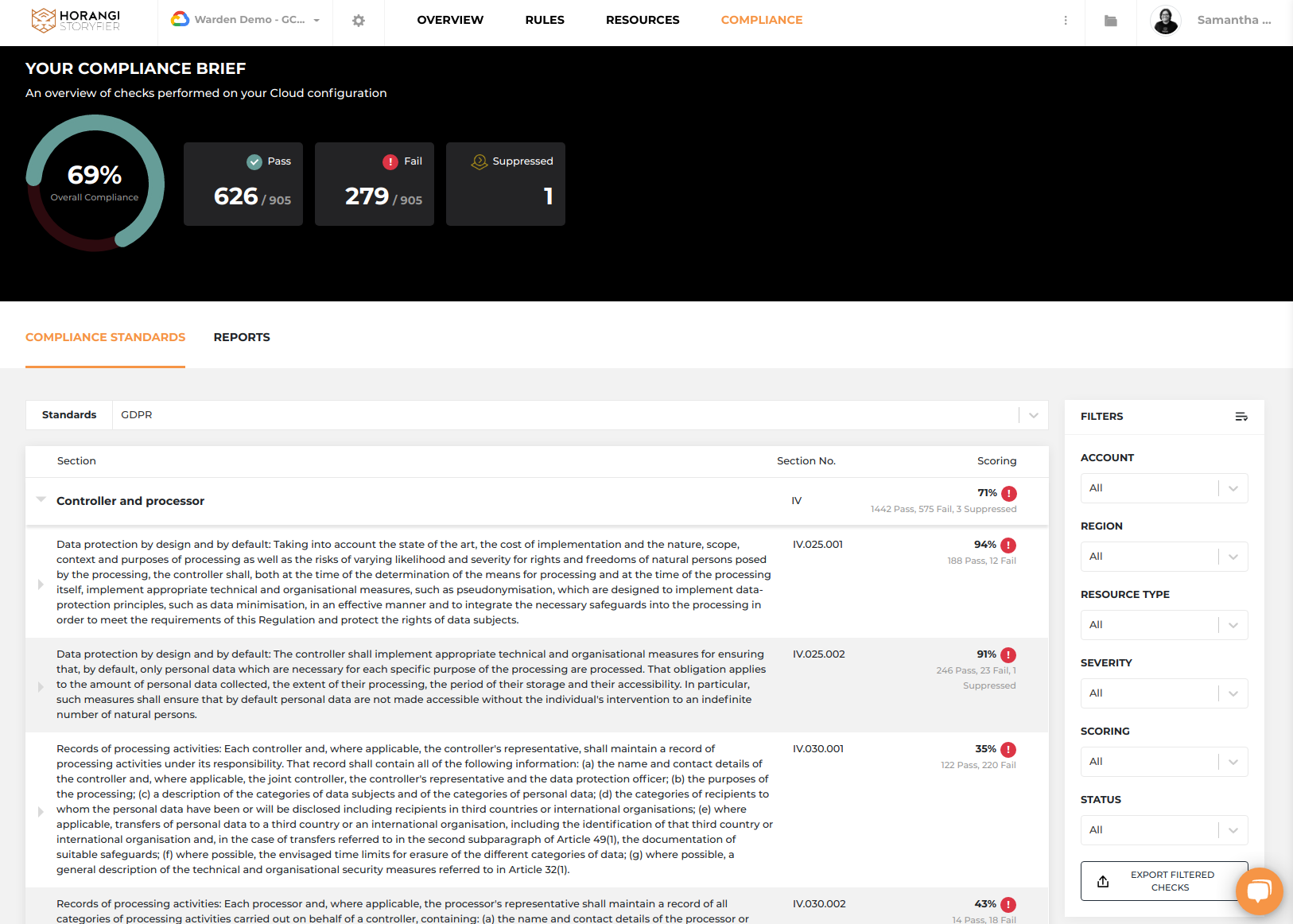
Dashboard — Warden Compliance Brief
GDPR View
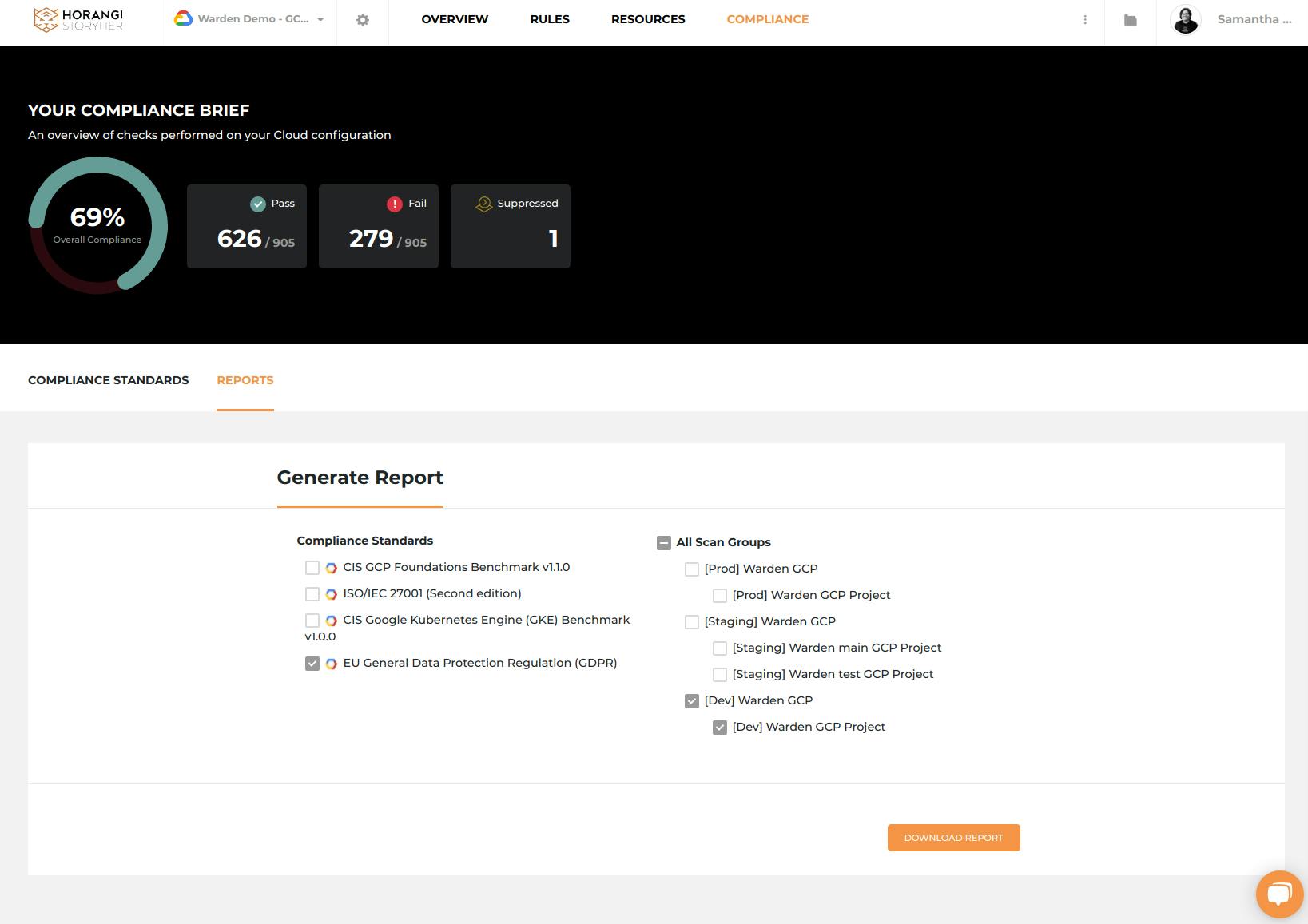
Generating A Compliance Report
Keep a lookout for our next launch event for Horangi Warden. We look forward to sharing more in the coming months.




