Why Do You Need Warden IAM Asset Inventory?
While technical teams are increasingly adopting the multi-cloud strategy for multiple reasons like cost efficiency or operational flexibility, making it increasingly challenging for security teams to keep track of the cloud assets being created, modified or even opened up to public access. This dynamic rate of speed at which things change in the cloud makes it almost impossible for them to answer a series of essential questions such as:
- How can teams attest to compliance and security metrics if they do not reliably identify all assets within their cloud environments?
- How can teams identify the critical assets and never lose sight of these assets?
- Among the overwhelmingly long list of misconfigurations, security risks and alerts discovered, how can teams quickly identify and safeguard the critical resources associated with them?
What Value Will This Feature Add?
Warden’s team has been working hard to roll out Warden Asset Inventory with an aim of providing centralized asset management, where your most sensitive assets are discovered automatically. You can get immediate value here, where your assets will be highlighted with vulnerabilities and security alerts. They will be prioritized for quick identification, so you never lose sight of the critical assets that might lead up to a breach.
Automated Discovery
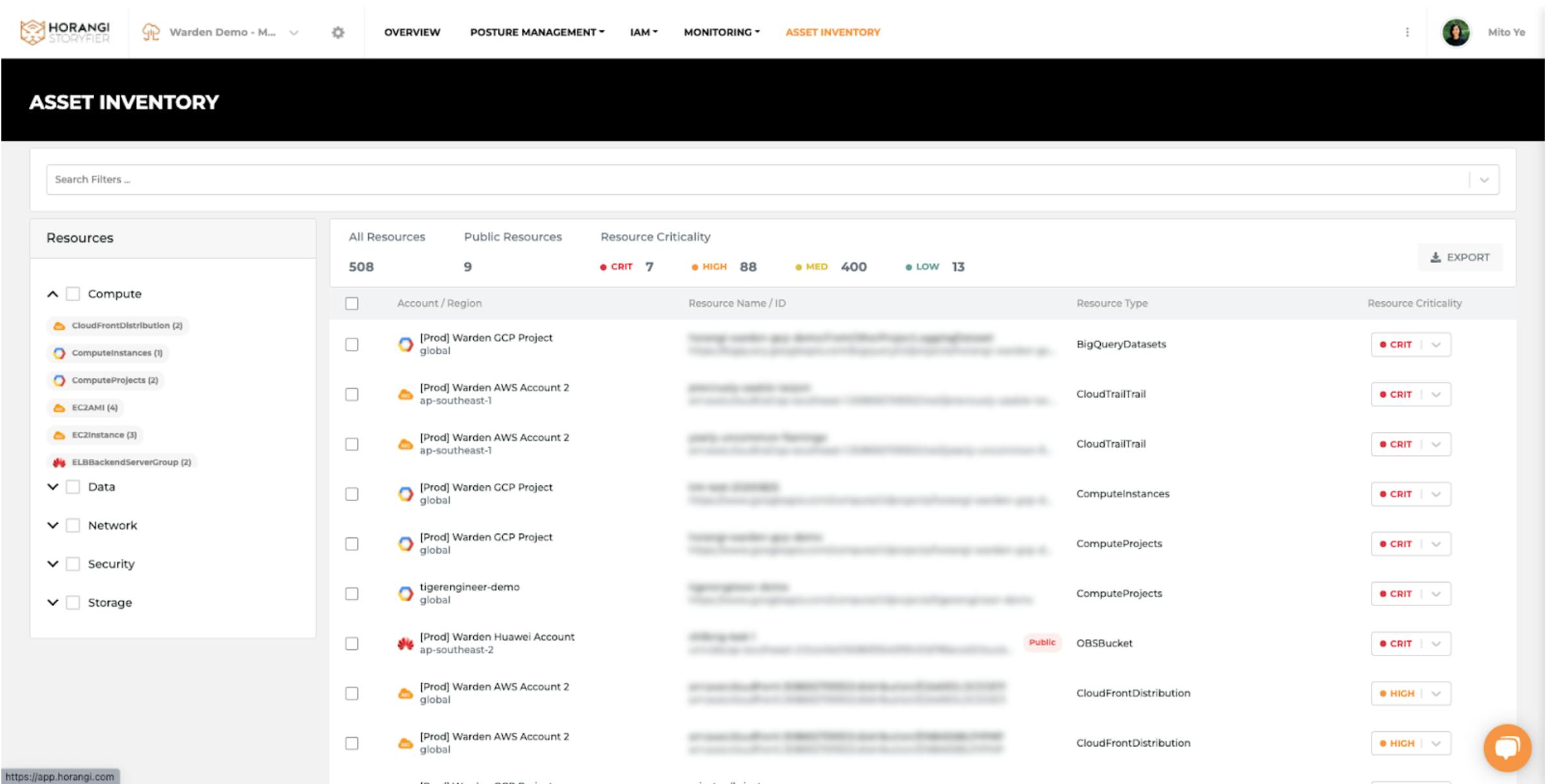
Within minutes of setting up a Warden scan account, the resources discovered in the accounts scanned are automatically updated and added to the Asset Inventory. This list of assets is automatically updated based on your preferred scanning frequency.
If you have a multi-cloud environment, Instead of having to go through each individual cloud console to extract or export the list of assets, you can do so in a single place on Warden. We are constantly expanding our coverage and adding as many Cloud Service Providers to help you prioritize and fix vulnerability at build speed. Currently, we support AWS, GCP, Microsoft Azure, and Huawei Cloud.
(Note: Currently only the cloud resources are part of the Asset Inventory. We are working on adding more cloud assets to the Inventory list. In case there’s a pertinent need, please feel free to reach out to us if there's any other types of assets you would like to see in here)
Prioritize Critical Resources
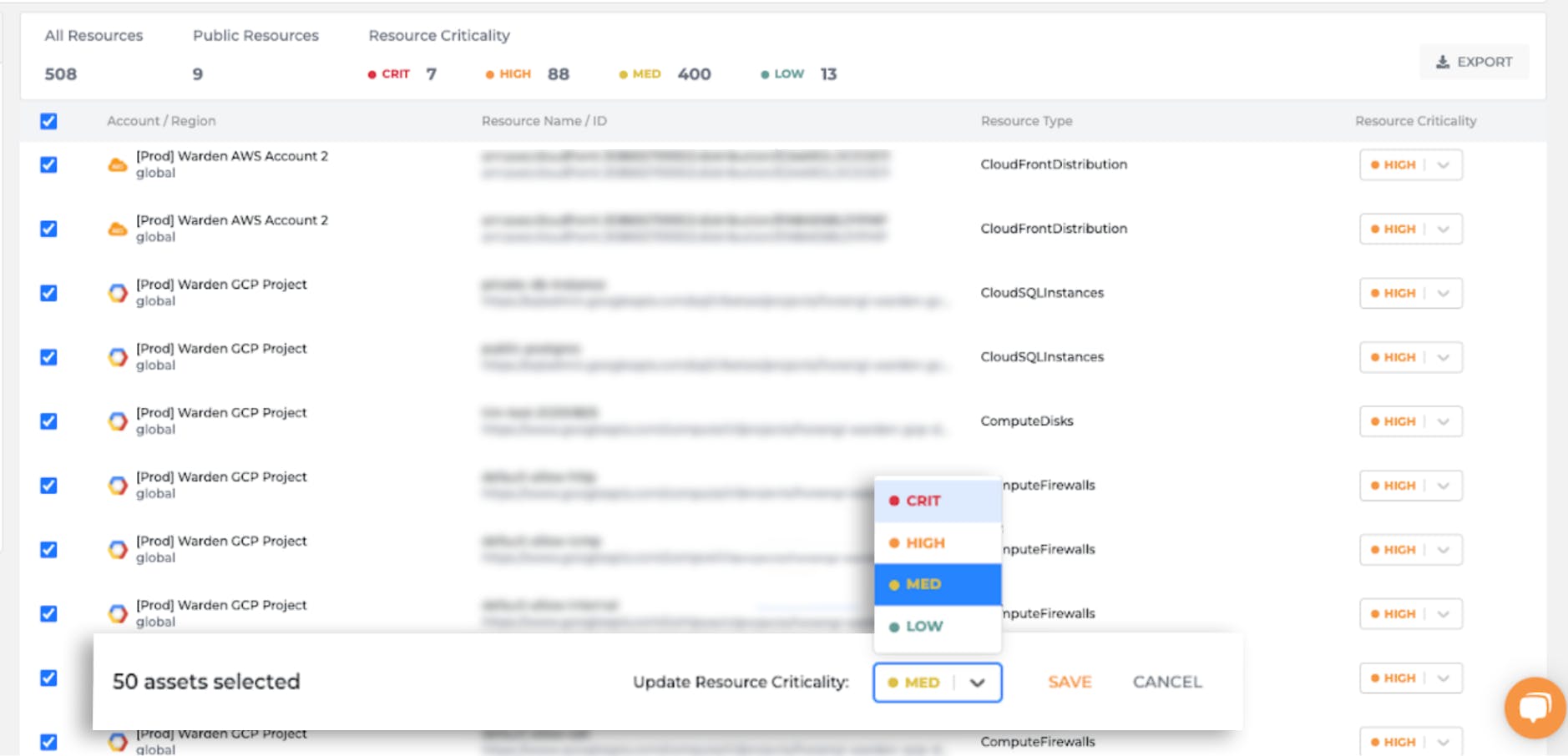
Warden IAM aims to streamline access management for all of your cloud infrastructure. However, we understand that not all assets are equal from a security standpoint. Some of them you wouldn’t want to lose sight of at all. These could be your assets which correspond to the production environment or resources where your most sensitive customer data is stored. We created this feature to help you prioritize the ones which take precedence over other assets. This gives you the freedom to focus and fix the ones where vulnerabilities and security loopholes could be catastrophic for your business.
Tip: You can also easily deprioritize the assets to come back and review later or their associated risk findings.
Warden Asset Inventory allows you to add in that criticality context so that:
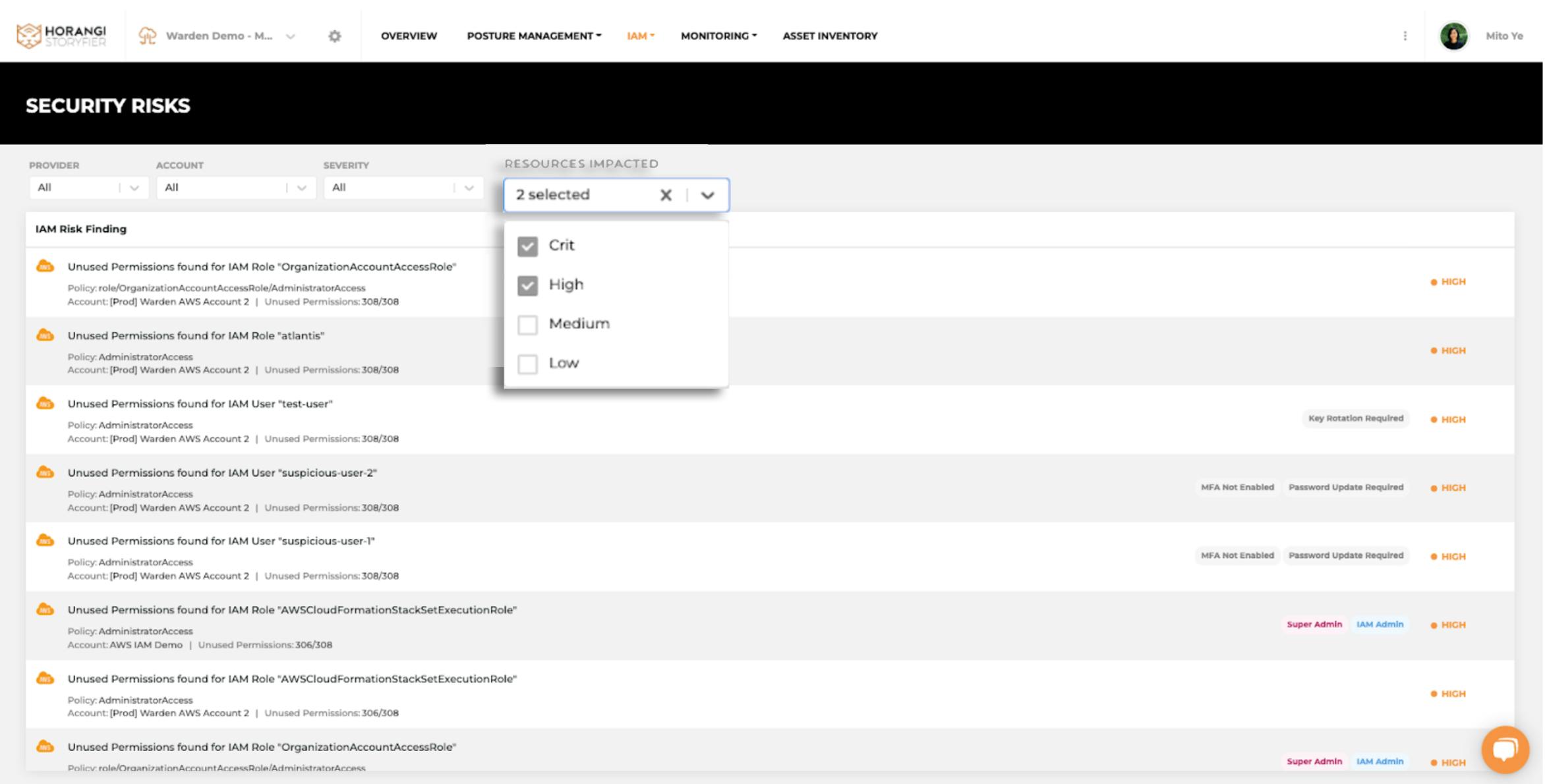
- You will never lose sight of the most important assets from the Inventory. Because the Asset Inventory list is ranked based on the criticality flagging from the most critical to high, medium, and low priority.
- You can quickly identify and prioritize the Warden IAM security risk findings that are impacting your critical resources. Get them fixed first before the attackers have the chance to compromise any of your critical assets.
- Bonus: We are working on rolling out another milestone feature to identify and prioritize the Warden CSPM findings and monitoring alerts that are impacting your critical resources soon.
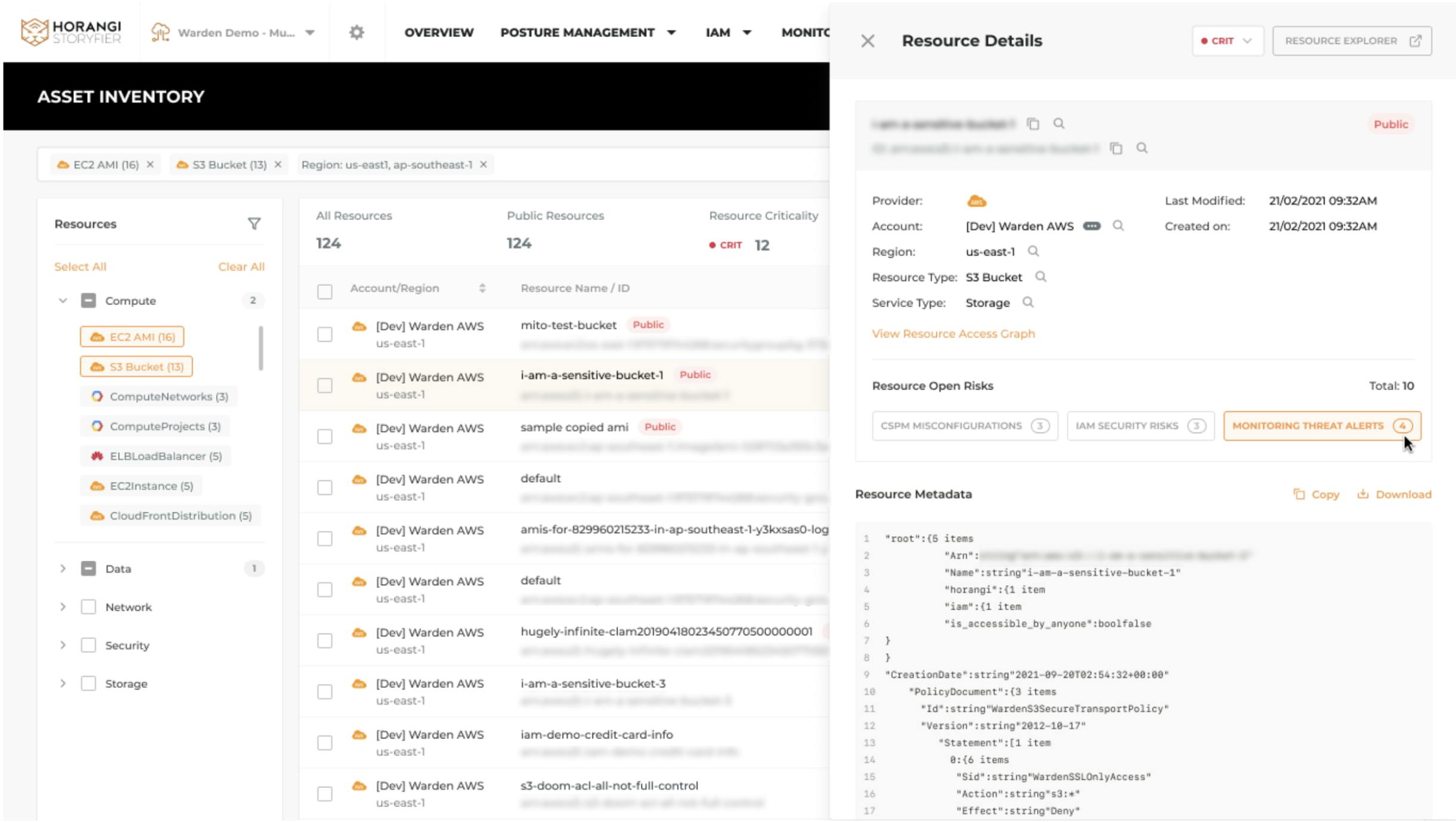
Vulnerability and Security Alerts Association
Security risks and alerts are mostly related and often neglected. This could be due to the sheer volume of alerts that you get in a day, making it impossible to look at all of them with microscopic clarity. But in a dynamic cloud environment, we must remember that threat alerts are often the surface symptoms while the misconfigurations or excessive permissions granted in IAM are among the culprits or loopholes for the attacks.
Therefore, during the security review, we encourage you to check through all the CSPM misconfigurations, IAM Security Risks and Monitoring threat alerts that are associated with the assets. This is especially important for your critical assets.
Conclusion
Asset Inventory is here to help you have a single pane of glass looking into your assets, to flag out the critical ones and start reviewing all the vulnerabilities and security alerts associated with them today! If this is something that you would like to try, then drop a line here.




