Warden Threat Detection on GCP
In our last blog, we talked about Warden Real-time Threat Detection monitoring for Amazon Web Services (AWS). Starting this October, we are excited to extend Warden Threat Detection support for organizations using GCP! Our flagship product Warden, equipped with cutting-edge Threat Detection can detect high-risk infrastructure changes indicative of Defense Evasion, Persistence, Exfiltration, etc. All the alerts are mapped to the MITRE ATT&CK framework.
The Need: Native Cloud Provider Tools are NOT Enough
Most cloud providers are equipped with some solutions for detecting threats such as GuardDuty for AWS, Security Command Center for GCP, etc. However, these native tools leave some eminent gaps in your cloud security stack. They are often simple to configure for very simple, basic deployments and cover an organization’s basic security needs but have gaps when it comes to more complex IT infrastructures, such as multi-cloud environments or a mix of cloud and on-premise security. Additionally, they can be costly when considering the need to hire and maintain in-house cloud security experts to continuously configure and maintain security tools. Here’s a rundown of some highlights:
- Rules are not exactly customizable: All the rules and severity of the findings are defined only by the cloud providers and you cannot change them based on your security setting needs.
- Tools are usually focused only on detection: You need to comb through raw logs for the investigation to find out the context, which is extremely manual and time-seeking.
- Cost can be humongous: These native tools are often not a part of the basic subscription. For example, in GCP Security Command Center, the threat detection features are not included in the standard subscription package, so you have to pay extra to upgrade to premium for access, which eats up your cloud security budget, without giving you access to customization and investigation capabilities.
The Solution: Warden to the Rescue
A. Intelligent detection protects you from potential threats
1. Warden Threat Detection is enriched with threat intelligence: Let's take an example for GCP, in addition to audit logs, we also detect connections from suspicious IPs or anything from those IPs that have been flagged as abusive, malicious, or anonymous. To give you Real-time threat alerts, all on your unified dashboard.
2. A step ahead with high-risk infrastructure changes alerts: We send you alerts anytime Warden detects any high-risk change in your infrastructure settings. This could be indicative of Defense Evasion, Persistence, Exfiltration, etc.
Monitoring Alerts in Warden Threat Detection
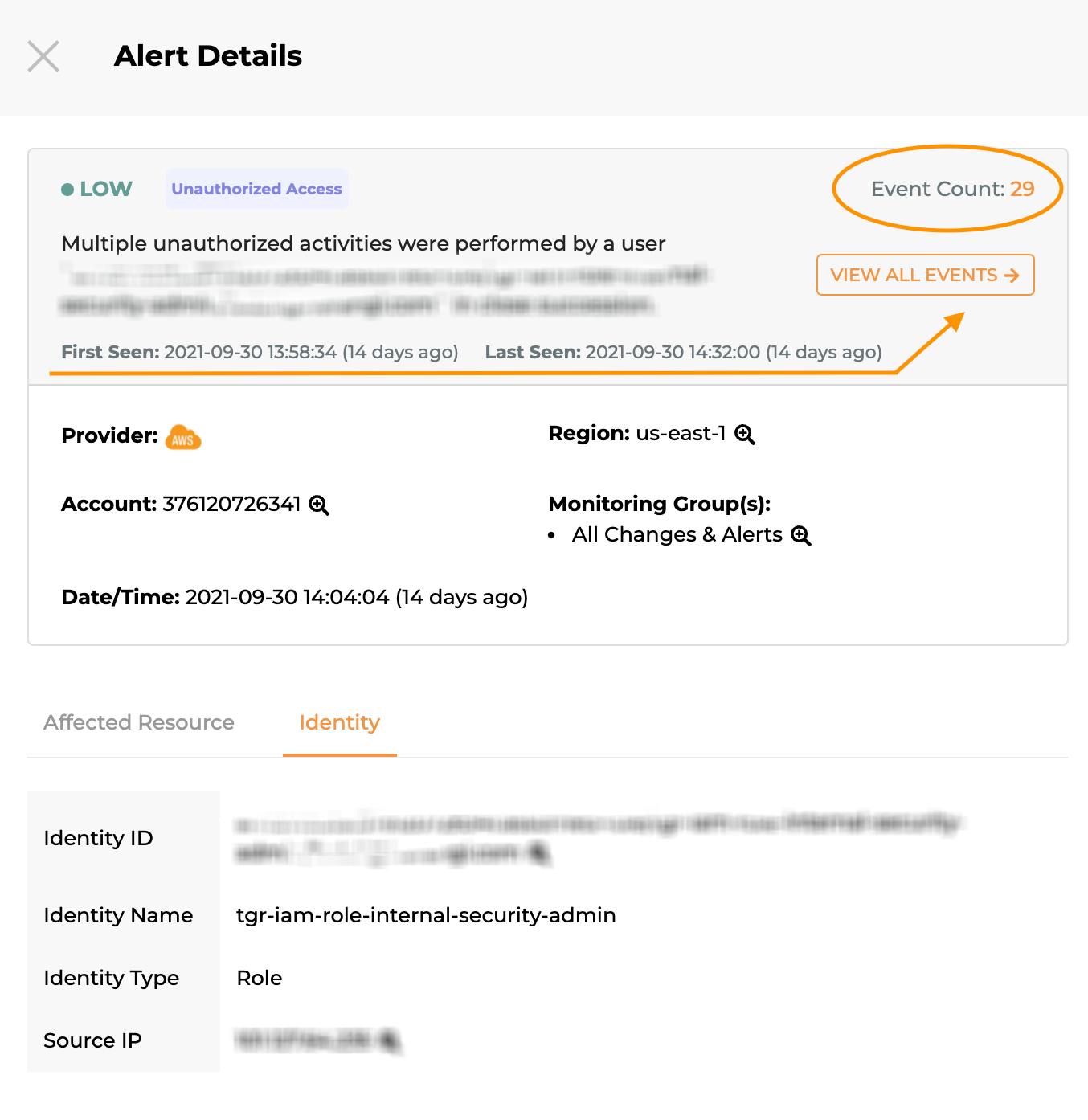
3. Detect Suspicious user activity & respond faster to what matters the most: Warden watches your infrastructure like a hawk and only alerts when it detects any abnormality to reduce the noise. It shows one aggregated alert with all related events, as well as the number of occurrences of when such an abnormality was first and last seen. This saves you time and energy of combing through a zillion alerts and only focusing on what matters the most, right off the bat.
B. Fine-grained monitoring configuration for efficiency
1. Flexible grouping of alerts with monitoring scope configuration: You can configure the alerting scope to focus on what matters to your security needs, like specific to cloud environments, account regions, or resource types.
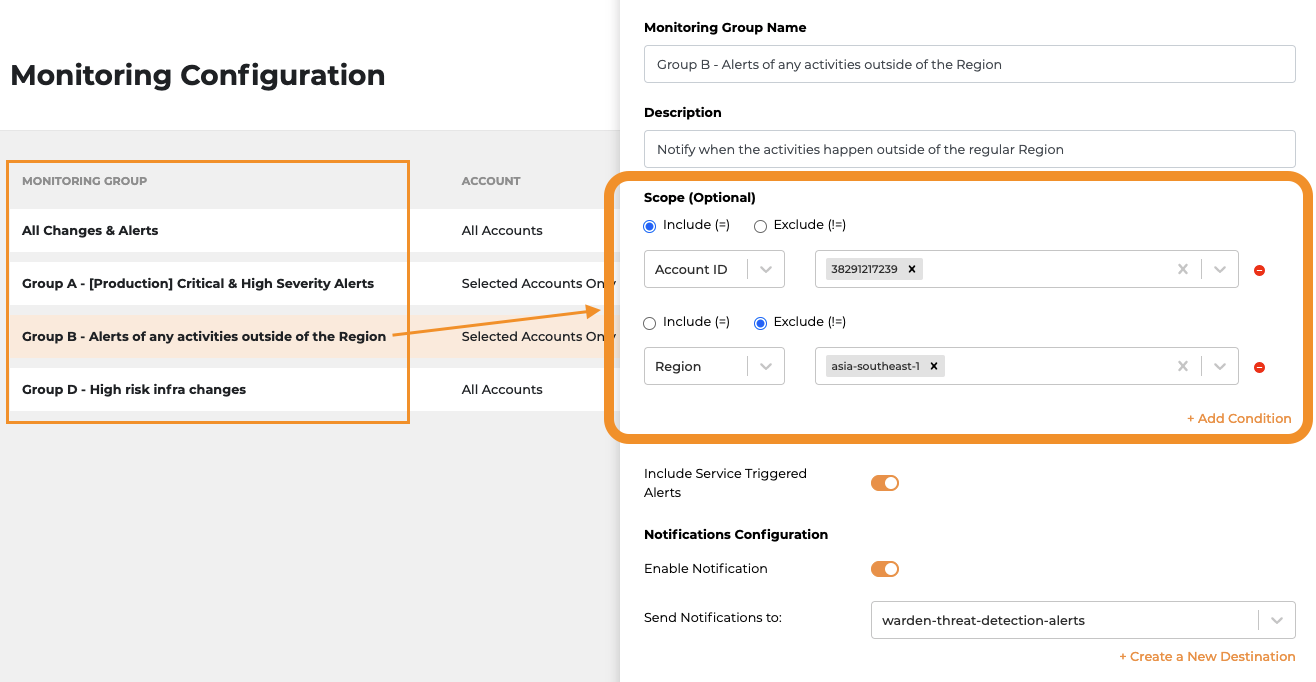
Define Scopes in Monitoring Group Configuration
2. Reduce noise with rule level configuration: With rule level configuration you can enable or disable the rules and change the severity accordingly based on your organization’s security needs. This can help you to prioritize which alerts to address, while the security team focuses only on the alerts they care about the most.
Change severity and enable/disable rules in Rule Configuration
3. Accelerate investigation with normalized logs and quick filtering: All alerts on the Warden Threat Detection dashboard are provided with affected resources and related normalized events that can be directly used for investigation. It helps to accelerate the investigation while you can filter (with a click) on any of the key attributes that you're going to be looking for whether that is a cloud account, region, resource, a specific user, or an IP.
Warden Threat Detection Investigation Demo
C. Beyond Real-time Threat Detection
1. All-in-one security management: Warden Threat Detection together with CSPM and IAM can secure your cloud environment 24/7. Warden is the only human-centric, agentless security platform that sets up in minutes and delivers only relevant security alerts at the right time, giving organizations the freedom to innovate in the cloud.
2. Real-time alerts delivered over your preferred channel of communication: You can configure your organization’s slack channel to receive notifications when critical alerts occur. It is also possible to connect different slack channels for different alert groups, to easily direct those alerts towards the team handling that scan group. You can also configure an outbound integration with Google Cloud Pub/Sub to receive real-time alerts via Pub/Sub subscriptions.
Conclusion
With a whopping $3.86M being the global average total cost of a breach just last year, we can safely say that prevention is never enough, you need real-time threat monitoring to predict and remediate potential vulnerability issues before they occur. You can easily get started with Warden by dropping us a line here.




