Humble Beginnings of Hacking
For all the headlines made today by massive data breaches, ransomware and cyberwarfare, the world’s very first cyber hack started as an innocuous research project fueled by passion.
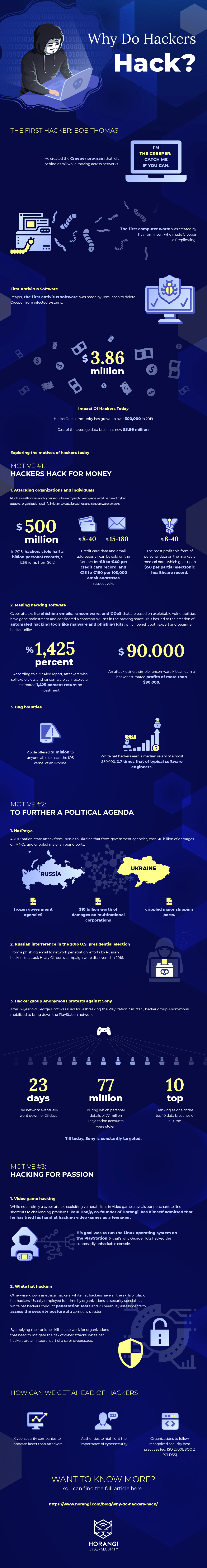
Bob Thomas, the unofficial founder of hacking, had realized it was possible for a computer program to move across networks while leaving behind a trail. He designed a program known today as Creeper that traveled between Tenex terminals on the early ARPANET. The program caused infected systems to print the message: I’M THE CREEPER: CATCH ME IF YOU CAN.
This then caught the interest of Ray Tomlinson, who tinkered with the program and made it self-replicating, creating the first computer worm. Seeing if he could create a counter to Creeper, Tomlinson wrote another program called Reaper. Reaper is known today as the inaugural version of antivirus software after it was able to successfully delete Creeper from infected systems.
Hackers have evolved in number and motive from the humble days of Bob Thomas and Ray Tomlinson, with the HackerOne community growing to over 300,000 in 2019.
Now that the cost of the average data breach to companies worldwide has risen to $3.86 million, it is more pertinent than ever to explore just what motivates hackers to hack.
Motive #1: Hackers Hack For Money
Hacking is a lucrative business. With the cybercrime economy reportedly being already worth as much as the GDP of the entire Russia and the low levels of traceability, we can expect hacking to continue growing as a highly profitable industry.
There are many ways in which a hacker can make money. The income sources of a hacker include:
1. Attacking organizations and individuals
Much as authorities and cybersecurity are trying to keep pace with the rise of cyber attacks, organizations still fall victim to data breaches and ransomwareransomware attacks. In 2018, hackers stole half a billion personal records, a 126% jump from 2017. Credit card data and email addresses all can be sold on the Darknet for €8 to €40 per credit card record, and €15 to €180 per 100,000 email addresses respectively. The most profitable form of personal data on the market is medical data, which goes up to $50 per partial electronic healthcare record.
2. Making hacking software
Cyber threatsCyber threats such as phishing emails, ransomware, and DDoS that are based on exploitable vulnerabilitiesexploitable vulnerabilities have gone mainstream and considered a common skill set in the hacking space. This has led to the creation of automated hacking tools like malware and phishing kits, which benefit both expert and beginner hackers alike.
According to a McAfee report, attackers who sell exploit kits and ransomware can receive an estimated 1,425 percent return on investment.
In fact, Trustwave estimates that 0.5% of infected ransomware victims on a 20,000 user a day website typically agree to pay the ransom. For a ransom of $300, this adds up to estimated profits of more than $90,000 with the use of a simple ransomware kit.
3. Bug bounties
White hat hacking to help organizations identify exploitable vulnerabilities is also growing in popularity. Apple was willing to pay $1,000,000 to anyone able to hack the iOS kernel of an iPhone without requiring any clicks by the user.
White hat hacking is growing to become an attractive career path, possibly earning more than black hat hackers. According to PayScale, white hat hackers earn a median salary of almost $80,000, 2.7 times that of typical software engineers.
Motive #2: To Further A Political Agenda
When hackers aren’t motivated by money, they often do so for a cause. Hacktivism is the act of hacking a website or computer network in an effort to convey a social or political message.
As with all nations, competition and division are natural by-elements of opposing ideologies and conflict. In the past, war was waged on land. But in recent history, with core government processes being managed digitally, warfare is transiting to the online medium.
Below are some prominent hacktivism cases in recent times:
1. NotPetya
What was meant to be a nation-state attack from Russia to Ukraine ended up with collateral damage including frozen government agencies, $10 billion worth of damages on multinational corporations and crippled major shipping ports.
An attack aimed at Ukraine ended up striking Maersk, and an attack on Maersk struck those affiliated with it. This chain effect was so extensive it returned to strike the Russian state oil company Rosneft.
2. Russian interference in the 2016 U.S. presidential election
Multiple efforts made by the Russian hackers to harm the presidential campaign of Hilary Clinton were discovered in 2016. Among the cyber attacks that the Russian hackers employed were a phishing email masked as a Google alert and a penetration of the computer network of the Democratic National Committee.
3. Hacker group Anonymous protests against Sony
17-year old George Hotz was sued by Sony for jailbreaking the PlayStation 3 and releasing the code to the public. In response to the alleged injustice, the hacker group Anonymous launched a campaign to bring down the PlayStation network. The network eventually went down for 23 days, during which personal details of 77 million PlayStation accounts were stolen, ranking as one of the top 10 data breaches of all time. Till today, Sony is constantly targeted.
Motive #3: Hacking For Passion
Like how Bob Thomas and Ray Tomlinson started the hacking and cybersecurity loop, not all hackers have malicious intent. Some hack for the thrill of breaking things and just because they can, to hone their skills. Existing on the Internet are vigilantes who discover vulnerabilities in systems on their own accord and then report it to the system owners, sometimes for a fee. This group is sometimes known as gray hat hackers.
Popular forms of non-malicious hacking include:
1. Video game hacking
While not entirely a cyber attack, exploiting vulnerabilities in video games reveals our penchant to find shortcuts to challenging problems. Paul Hadjy, co-founder of Horangi, has himself admitted that he has tried his hand at hacking video games as a teenager.
The most well-known case is, again, George Hotz, who hacked into the supposedly unhackable PlayStation 3 gaming console. Hotz’s motive for this was to run the Linux operating system on the machine that Sony had earlier removed in spite of popular demand.
2. White hat hacking
Otherwise known as ethical hackers, white hat hackers have all the skills of black hat hackers. Usually employed full-time by organizations as security specialists, white hat hackers conduct penetration tests penetration tests and vulnerability assessmentsvulnerability assessments to assess the security posture of a company’s system.
By applying their unique skill sets to work for organizations that need to mitigate the risk of cyber attacks, white hat hackers are an integral part of a safer cyberspace.
Closing Thoughts
Like any other passion, hacking — white, gray, or black — epitomizes the simple human desire to find creative solutions to the toughest challenges. However, as more devices and machines get connected to the Internetas more devices and machines get connected to the Internet, hackers wield more power than ever to cause damage.
The onus falls on cybersecurity organizations to innovate faster than attackers, working together with authorities to educate the public on the importance of cybersecuritycybersecurity.
If you enjoy testing systems to their breaking point, and seek joy in discovering vulnerabilities and/or in building better systems — Horangi wants you. We’re always on the lookout for exceptional talent.