Accelerating Cloud Adoption = More Probable Exposed Attack Surface
The mass shift to remote work ‒ as a direct result of the COVID-19 pandemic ‒ has served as one of the key catalysts in the already accelerated adoption of cloud computing solutions in 2020 - 2021. And with rapid cloud adoption comes a higher risk of cyber attacks, as it is almost impossible to secure all cloud workloads, making them breach-safe with just native cloud security solutions.
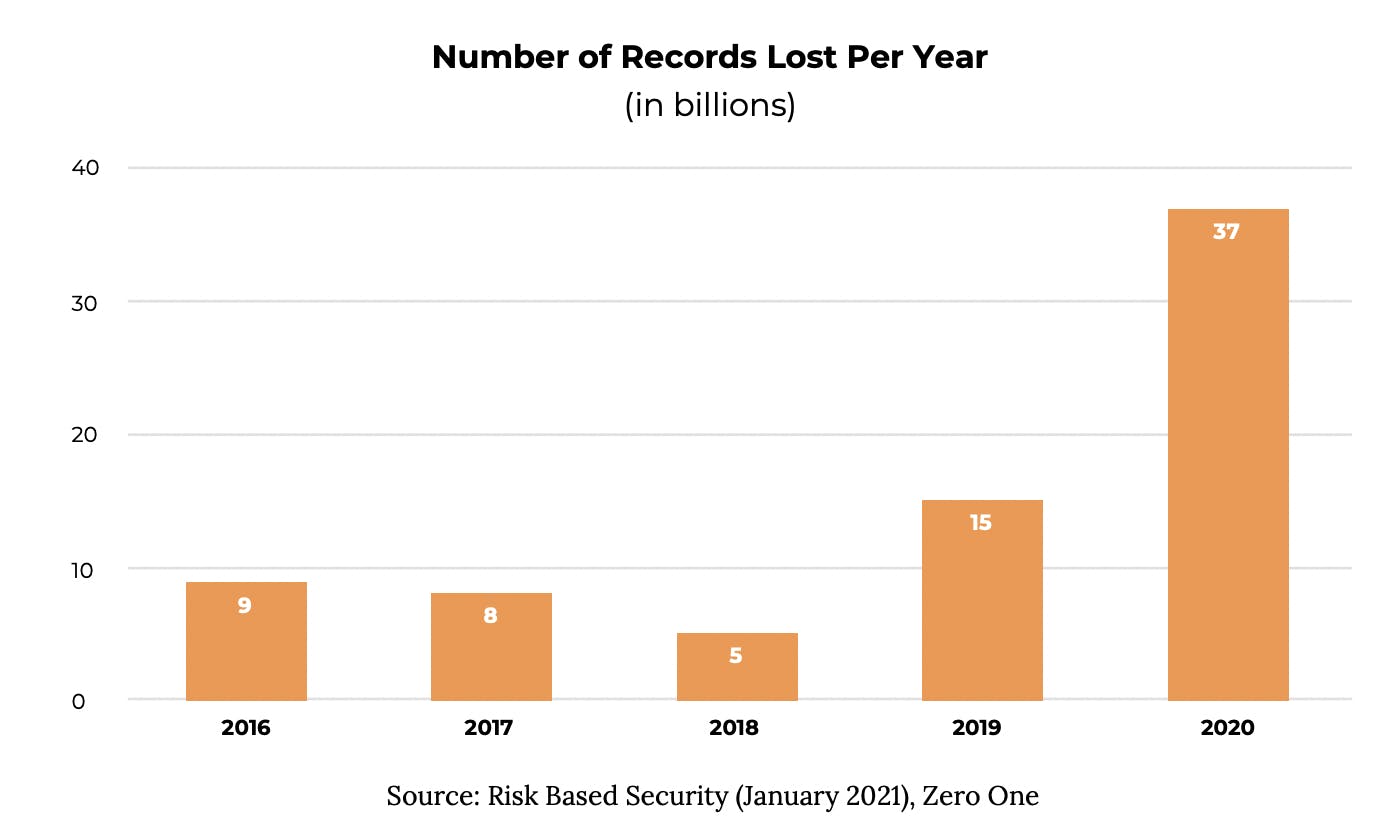
37 billion records were exposed in 2020 by data breaches, of which a substantial portion stemmed from insecure cloud infrastructure - according to Risk Based Security Firm’s latest report.
And with cyberattacks on the rise, it is no surprise that cloud security is a top priority for all cloud-native organizations. But IT and security teams often struggle to choose the right strategy because there are so many tools and services to help secure cloud workloads.
The Conundrum: Native Cloud Security Tools or Third-Party Tools?
There are two categories of solutions available to secure cloud workloads: cloud-native security tools supplied by the cloud service providers, and third-party security tools from other companies or, in some cases, open-source projects. But which type of cloud security tool is best? The answer depends largely on the specific cloud architecture and the nature of an enterprise's security needs.
Native Cloud Security Solutions May Cover Basic Security Needs But Can Have Gaps
The top three cloud service providers for Q4 2020 are Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP) and each provides its own suite of native cloud security tools. They are often simple to configure for very simple, basic deployments and cover an organization’s basic security needs but have gaps when it comes to more complex IT infrastructures, such as multi-cloud environments or a mix of cloud and on-premise security. Additionally, they can be costly when considering the need to hire and maintain in-house cloud security experts to continuously configure and maintain security tools.
Factors When Choosing Native or Third-Party Cloud Security Solutions
In choosing between the two, decision-makers should take into consideration the company’s current resources and cloud security expertise, current IT infrastructure, the expected usage of the cloud, the complexity of the business as well as its regulatory environment, and the sensitivity of data being handled. For companies with relatively simple business operations in a single cloud environment, native cloud security could be sufficient. However, for companies in complex and highly regulated industries such as finance, healthcare, services, and government, third-party cloud security can provide better security coverage.
To read the complete list of factors that you should consider, download the whitepaper here which gives you access to industry insights and key concepts your team can refer to as you build your cloud security strategy for 2021 and beyond.





