
Stop Breaches with Horangi's Cloud Security Posture Management
Reduce the headcount required to hire a cloud security team by 70% to do manual checks by automatically identifying and mapping infrastructure configurations to compliance standards like MAS TRM, OJK, SOC 2, GDPR, or your custom compliance needs, in a 10-minute no code set up.






Transform your CSPM journey in minutes




Reduce Time to Market, and Increase Confidence in Digital Transformation.
Reduce Time to Market, and Increase Confidence in Digital Transformation.
Reduce the time-to-market for modernizing your infrastructure by automating the discovery of misconfiguration in the cloud. Increase confidence to pave way for multi-cloud digital transformation through clear reporting & elimination of data security risks.





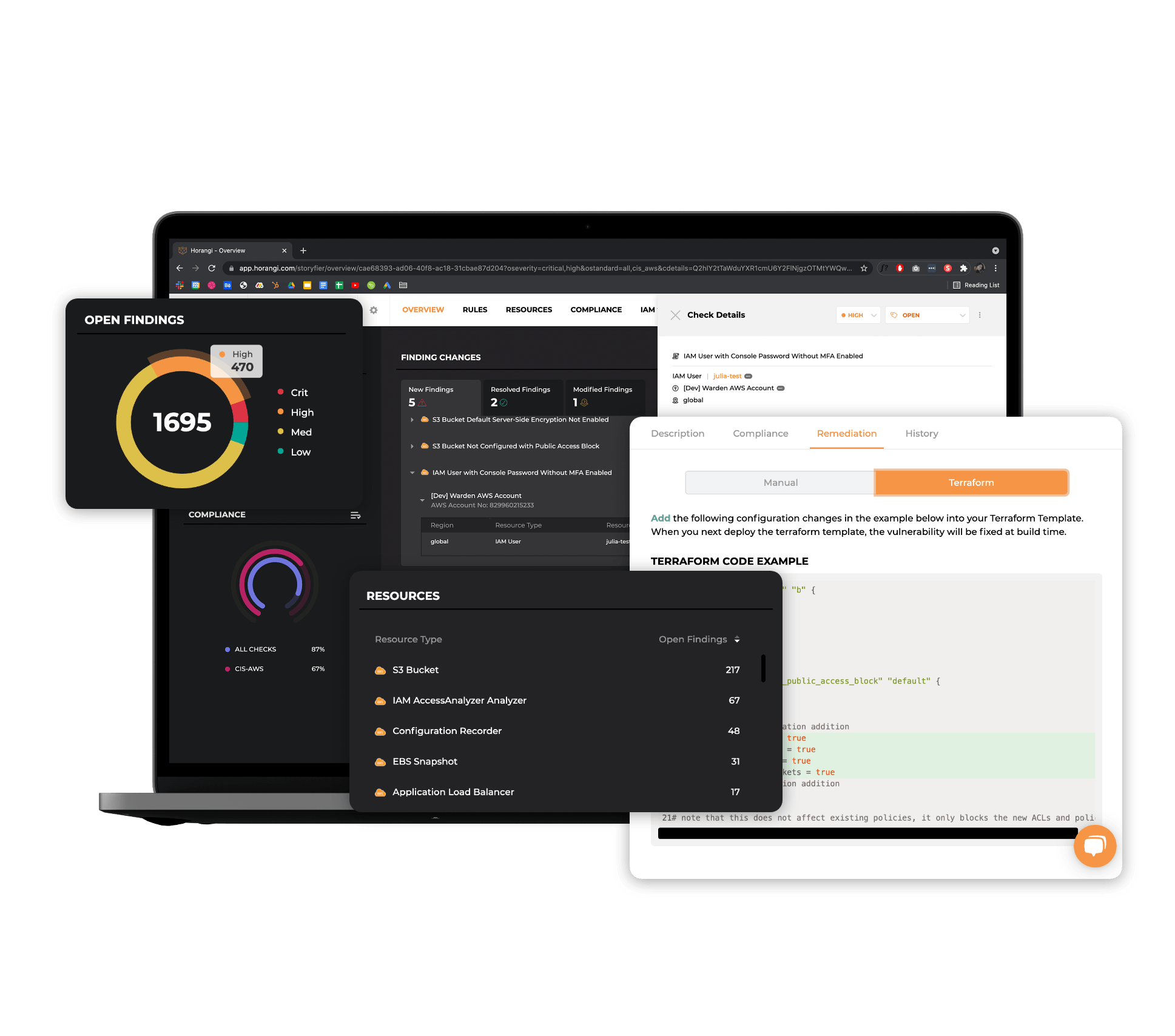
End-to-end cloud control from one agentless view
End-to-end cloud control from one agentless view
Complete visibility of all your VMs, serverless, storage buckets, and data lakes to tell you what’s in your multi-cloud environment, what your security gaps are, and how to improve security posture.
Automated cloud-native security integration with deeper and faster cloud inspection
Automated cloud-native security integration with deeper and faster cloud inspection
Resolve misconfigurations, IAM risks, and compliance violations instantly without having to rely on multiple tools. Identify weak credentials, lateral movement risk, excessive permissions and more in real time on the Warden platform.

Authority to Operate (ATO) on AWS Program
The Authority to Operate (ATO) on AWS Program helps AWS Partners meet their customers’ authorization needs, whether it be architecting, configuring, deploying, or integrating tools and controls. AWS supports businesses globally that need to meet security, privacy, and compliance requirements for healthcare, privacy, national security, and financial sectors.

Authority to Operate (ATO) on AWS Program
The Authority to Operate (ATO) on AWS Program helps AWS Partners meet their customers’ authorization needs, whether it be architecting, configuring, deploying, or integrating tools and controls. AWS supports businesses globally that need to meet security, privacy, and compliance requirements for healthcare, privacy, national security, and financial sectors.

Built-in compliance automation recognized by Gartner
Easy access to evidence of compliance with plug-and-play mapping of technical controls for faster compliance audits across multiple standards.

Built-in compliance automation recognized by Gartner
Easy access to evidence of compliance with plug-and-play mapping of technical controls for faster compliance audits across multiple standards.
Save on expensive cloud security hiring costs. Achieve compliance with ease. Try Warden for free today.
Save on expensive cloud security hiring costs. Achieve compliance with ease. Try Warden for free today.
Or complete the form below to request a 1-to-1 demo with a Warden specialist.
Explore Warden Features

Compliance Automation
Demonstrate cloud compliance with standards including ISO 27001, SOC 2, GDPR, and MAS-TRM.

Compliance Automation
Demonstrate cloud compliance with standards including ISO 27001, SOC 2, GDPR, and MAS-TRM.
Compliance Automation
Demonstrate cloud compliance with standards including ISO 27001, SOC 2, GDPR, and MAS-TRM.
Compliance Automation
Demonstrate cloud compliance with standards including ISO 27001, SOC 2, GDPR, and MAS-TRM.

Threat Detection
Threat Intelligence on Warden helps you gain unified visibility of all user activity, whether expected or suspicious.

Threat Detection
Threat Intelligence on Warden helps you gain unified visibility of all user activity, whether expected or suspicious.
Threat Detection
Threat Intelligence on Warden helps you gain unified visibility of all user activity, whether expected or suspicious.
Threat Detection
Threat Intelligence on Warden helps you gain unified visibility of all user activity, whether expected or suspicious.

Identity & Access Management (IAM)
Limit the impact of a potential breach by 80% and tackle increasing complexity in managing infrastructure entitlements in a multi-cloud setup.

Identity & Access Management (IAM)
Limit the impact of a potential breach by 80% and tackle increasing complexity in managing infrastructure entitlements in a multi-cloud setup.
Identity & Access Management (IAM)
Limit the impact of a potential breach by 80% and tackle increasing complexity in managing infrastructure entitlements in a multi-cloud setup.
Identity & Access Management (IAM)
Limit the impact of a potential breach by 80% and tackle increasing complexity in managing infrastructure entitlements in a multi-cloud setup.

Cloud Posture Management
Keep track of thousands of multi-cloud resources on a unified dashboard that prioritizes the security alerts you need, delivered in the way you prefer.

Cloud Posture Management
Keep track of thousands of multi-cloud resources on a unified dashboard that prioritizes the security alerts you need, delivered in the way you prefer.
Cloud Posture Management
Keep track of thousands of multi-cloud resources on a unified dashboard that prioritizes the security alerts you need, delivered in the way you prefer.
Cloud Posture Management
Keep track of thousands of multi-cloud resources on a unified dashboard that prioritizes the security alerts you need, delivered in the way you prefer.
Vulnerability Remediation
Pick your preferred method to fix threats and vulnerabilities with Warden's variety of quick and easy cloud security remediation solutions.
Vulnerability Remediation
Pick your preferred method to fix threats and vulnerabilities with Warden's variety of quick and easy cloud security remediation solutions.
Vulnerability Remediation
Pick your preferred method to fix threats and vulnerabilities with Warden's variety of quick and easy cloud security remediation solutions.
Vulnerability Remediation
Pick your preferred method to fix threats and vulnerabilities with Warden's variety of quick and easy cloud security remediation solutions.
DevSecOps Integration
Warden seamlessly integrates into your existing workflows, helping you work at build time.
DevSecOps Integration
Warden seamlessly integrates into your existing workflows, helping you work at build time.
DevSecOps Integration
Warden seamlessly integrates into your existing workflows, helping you work at build time.
DevSecOps Integration
Warden seamlessly integrates into your existing workflows, helping you work at build time.
Hear From Our Customers
![]()

"Warden gives us detailed insights into our AWS infrastructure, with easy action items. One-click remediation makes solving the majority of issues trivial, and the frequent addition of rules keeps us at the cutting edge of best cloud security practices. The UI itself is easy to navigate and use. Most importantly though - Horangi's customer service is exceptional. They are always willing to hear feedback, provide support, or discuss feature requests in their roadmap."
- Vinoo G, Chief Technology Officer

"Warden gives us detailed insights into our AWS infrastructure, with easy action items. One-click remediation makes solving the majority of issues trivial, and the frequent addition of rules keeps us at the cutting edge of best cloud security practices. The UI itself is easy to navigate and use. Most importantly though - Horangi's customer service is exceptional. They are always willing to hear feedback, provide support, or discuss feature requests in their roadmap."
- Vinoo G, Chief Technology Officer
![]()

"Warden supports multiple cloud providers. It is easy to integrate with a multi-cloud environment and use. It provides helpful insight into how to remediate cloud security issues in just a few clicks. Warden also supports multiple CIS standards, and the ability to export reports is beneficial as it allows us to share them with different stakeholders and auditors without the need to grant access to the platform."
- Vasco X, Senior Cloud Engineer

"Warden supports multiple cloud providers. It is easy to integrate with a multi-cloud environment and use. It provides helpful insight into how to remediate cloud security issues in just a few clicks. Warden also supports multiple CIS standards, and the ability to export reports is beneficial as it allows us to share them with different stakeholders and auditors without the need to grant access to the platform."
- Vasco X, Senior Cloud Engineer
![]()

"Warden has filtering options to filter by account, region, severity, or service type, which makes it very easy to look at the services that you are concerned about and drill down on the finer details. Remediation actions are also quite helpful to identify what actions need to be taken to fix the alerts. Visualizations on user permissions also make it easy to see who has access to what and if they really need it."
- Anonymous, Cloud Security Engineer

"Warden has filtering options to filter by account, region, severity, or service type, which makes it very easy to look at the services that you are concerned about and drill down on the finer details. Remediation actions are also quite helpful to identify what actions need to be taken to fix the alerts. Visualizations on user permissions also make it easy to see who has access to what and if they really need it."
- Anonymous, Cloud Security Engineer
![]()

"The way Warden helps to identify non-compliance to major industry standards and recommendations on how to resolve those issues is extraordinary, especially if you don't have a strong cloud security background."
- Anonymous, Head of Infrastructure

"The way Warden helps to identify non-compliance to major industry standards and recommendations on how to resolve those issues is extraordinary, especially if you don't have a strong cloud security background."
- Anonymous, Head of Infrastructure
![]()

"We really liked the detailed explanations about how to resolve the issues and how easy it was to manage the findings."
- Chad L, Cloud Technology Team Lead

"We really liked the detailed explanations about how to resolve the issues and how easy it was to manage the findings."
- Chad L, Cloud Technology Team Lead
![]()

"A cloud security solution for non-techies. Simple and easy to understand. Intuitive UI."
- Jane O, Compliance Lead

"A cloud security solution for non-techies. Simple and easy to understand. Intuitive UI."
- Jane O, Compliance Lead

