Scams are attempts to gain access to someone’s confidential information or money.
There are various scams which are running around these days, such as Phishing Email scams, Lottery scams, Fake Anti-virus Software, etc. You may think that you wouldn’t be a target? Well...You could be!
Lottery scams are common crimes which lures you to click the url in emails or text messages. It may state something as enticing as “You have won the Lottery” followed by “Please submit USD 500 to process your prize."
However… there's no lottery to be won.
Please do not enter any of your personal information or send money to criminals. Always check and verify the information you receive via e-mail or text message!

Your email or message may contain unsuspicious url something like https://URLYouMayHeard.com. However, when you hover your mouse cursor on the url, it may direct to attackers’ playground which looks very similar to original url. Also, those urls could be misspelled intentionally such as https://URLYouMayHerad.com. As these urls are pretending to be the target website, it is very hard to identify as you may notice this url is legitimate at first glance.
Phishing email/message scam is another common attack in Korea. These emails are typically fraudulent emails appearing to come from legitimate enterprises. Sometimes, via messenger applications. The scammer deceives victims into sending money to him as pretending to be their relatives or family. Some scammers even use the photo of your friends and ask for urgent help.
According to Finance Supervisory Service in Korea, messenger phishing cases have been reported 1,468 from the beginning of this year to early April and the estimated loss was 3.3 Billion KRW. This amount could be bigger than reported as some victims might not report the crimes.
The criminals have generally follows 3 steps.
- Hack the vulnerable websites first and seize users’ ID and passwords.
- Using victim’s credentials, hackers access to target portal. Then, they extracts victim’s friends information such as phone number and name through contact list.
- Based on this information, they create feigned accounts and ask their targets to send money to the hacker’s own account.
Most victims would have transferred money without hesitation. Had the victim call their friends to verify the request, this scam could have been avoided.
If you are still thinking you are too clever to be a victim, here is another case.
On 19th July, there were multiple posts regarding ICO on Steemit. It says that KakaoTalk, the most popular messenger application opened ICO of KON tokens in Kakao Networks webpage.
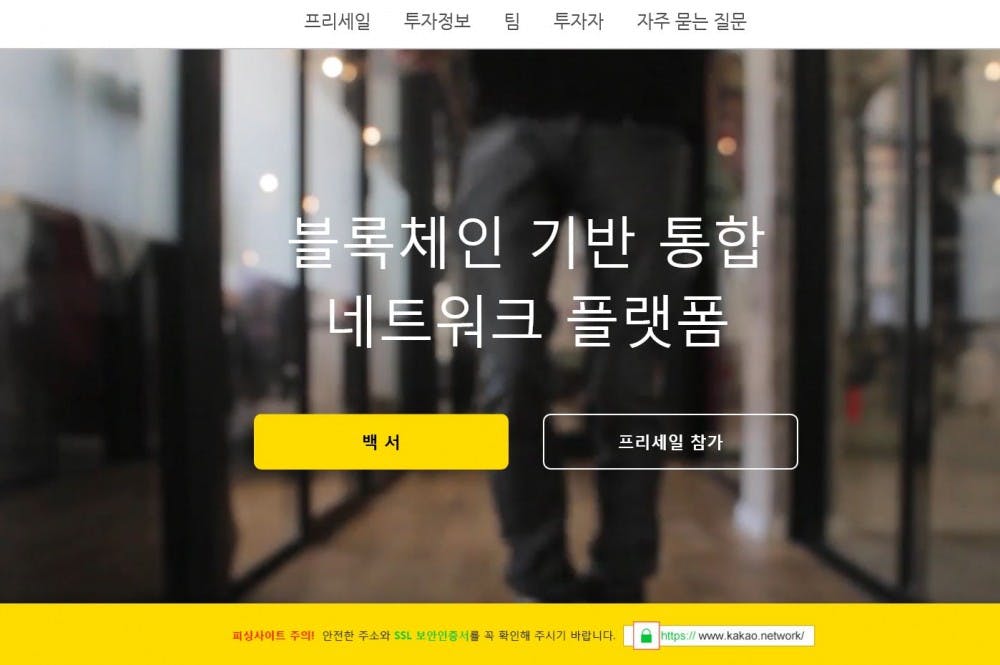
This website was using HTTPS and ironically had a phishing warning message on the main page. Also, there were more features giving trust to visitors which make viewers hard to believe this site is untrustworthy web page. CEO and some employers’ information were listed and the fake white papers seem so believable to non-coin experts.
These individuals easily believed this website built from KakaoTalk company and invested their money without further research. The total amount of loss reached into 60ETH within a few hours. General security tips which helps to prevent scamming issue was not effective in this case.
Nowadays, scammers have evolved and their tactics have become very subtle and difficult to recognize. They buy domains which seem related to the original websites, plan and organize marketing campaigns in social media platforms and pay for SSL to gain the trust of victims.
Can we stop being the fool?
Don’t believe what you see (Trust, but Verify)
If you see a URL in message or emails, check who sent it. Is it giving you a reliable information to be sure that sender is a authorized company you know? Please do your research.
There is no free lunch in this world.
What kind of transactions you are using?
Even in a seemingly real situation, do not easily send your money to your friends on websites you do not recognize.
When you really need to transfer money, use secure and traceable transactions.
Thinking of investing in an ICO?
Also, at the time of this article being written, there has been no official news that legitimate large enterprises lead ICOs.
If they did, it would've been covered in all relevant media and will be top-ranked on portals. That's one telltale sign something may be true.
Update your User ID and/or Passwords
I know this is hard to do. However, your commonly used ID/PW may already be in scammer’s hand. Try to use different PW per website. If you are using the same credentials across multiple websites, it increases the possibility of hackers' access to every services you use.
Being able to detect scammer’s actions might be a bit difficult. They employee techniques that prey on human vulnerabilities. This results in a false sense of urgency. Just be aware that you can be the one that scammer targets and bear in mind, scam phishing can happen to you with no indication at all.