What Is The Shared Responsibility Model?
For customers on public cloud service provider (CSP), security and compliance are not solely the responsibility of the CSP. Customers play an important role in cloud securitycloud security. In fact, both the customer and the CSP are responsible for cloud security, known as the Shared Responsibility Model.
In this model, both the cloud provider and the customer play a role:
- The CSP is responsible for “security of the cloud,” which includes all the physical infrastructure that runs the underlying cloud services
- The customer is responsible for “security in the cloud,” which includes the configuration chosen by the customer for their cloud resources.
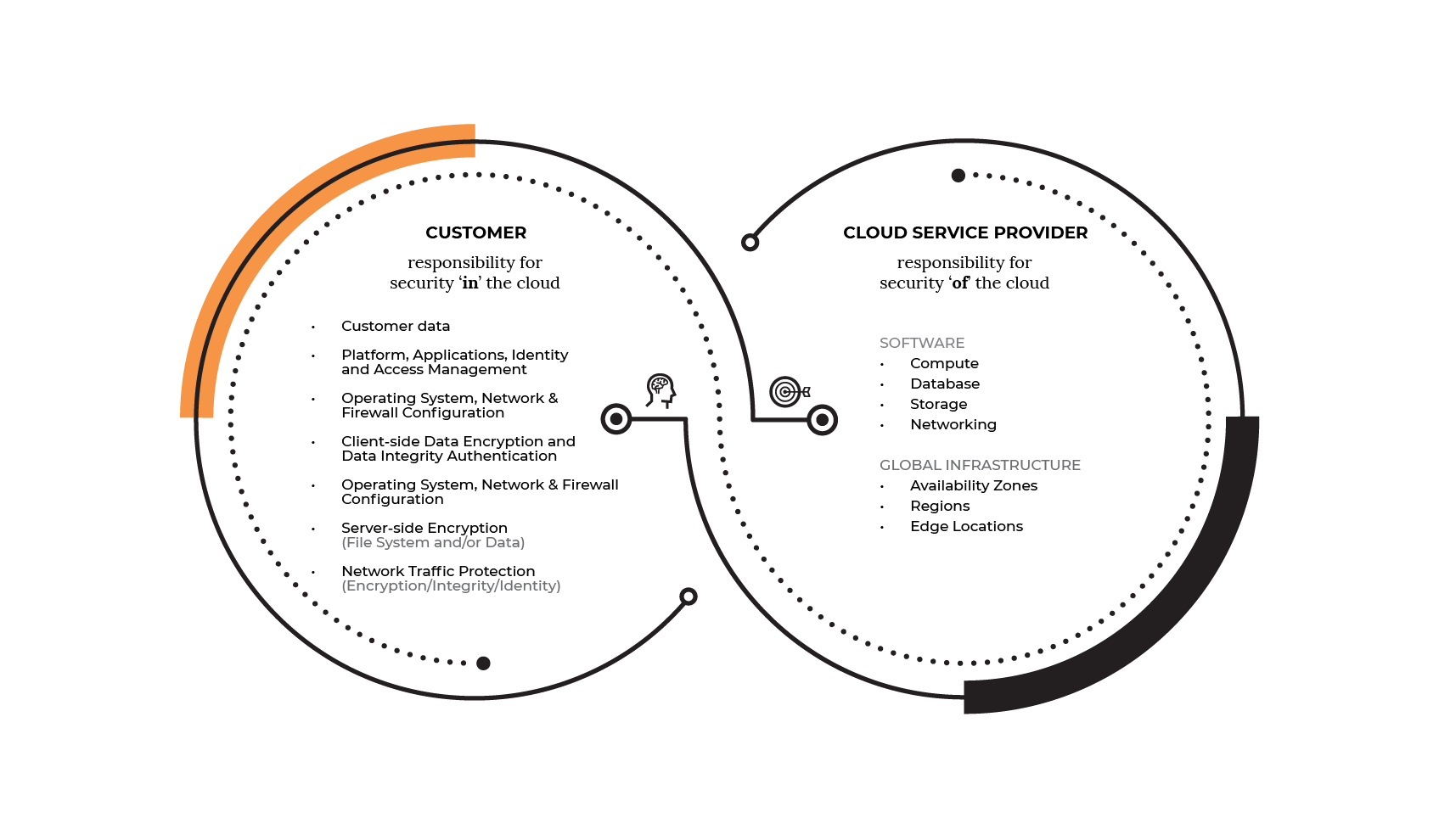
This differentiation of responsibility is commonly referred to as Security “of” the Cloud versus Security “in” the Cloud.
Why The Shared Model?
For customers with on-prem deployments, they are solely responsible for all aspects of the deployment, including things such as hardware, software, as well as security.
With a move to the public cloud, the customer's operational burden is reduced by taking advantage of the shared model. With this model, the CSP operates and manages the hardware, software, networking, and facilities, including the security “of” the cloud. Nonetheless, just as users in on-prem environments need to ensure correct configurations of their firewalls, access controls, and network, users in the cloud carry that same responsibility in configuring their cloud resources. Amazon S3, ElasticSearch, and RDS are examples of these resources.
What Are Customers Responsible For?
In the market, there remains confusion about the split of responsibility between CSPs and their customers. Reports by Barracuda Networks and Centrify note that almost two-thirds of cybersecurity experts believe that it is the CSP who should be protecting customer data in the cloud — which under the Shared Responsibility Model, is the customer’s responsibility.
For the customer, security “in” the cloud includes managing data, classifying assets, managing access, and cloud configurations. Cloud configuration management is the responsibility of the customer. Given the potentially high monetary cost of a single cloud data breach (eg, Capital One 2019 data breach) or a single cloud misconfiguration (eg. Accenture 2017 data leak), customers must take stock of secure configurations in their cloud environments.
How Can Customers Secure Their Cloud Environments?
Gartner notes that through 2023, at least 99% of cloud security failures will be the customer’s fault. Customers can reduce their risk by having an automated tool that checks for faults in the cloud environment. These are the same vulnerabilities that attackers scour the Internet to exploit, so it pays for organizations to look at automation tools.
A Cloud Security Posture Management (CSPM) tool is one such tool — a CSPM can monitor cloud environments to identify risky configurations and gaps in cloud security posture. Having this added visibility into public cloud environments also helps organizations to prevent costly compliance policy violations. Considering the majority of cloud data breaches are the result of simple misconfigurations, CSPMs such as Horangi Warden are seeing increased adoption in recent years.
Horangi Warden, A CSPM tool
Horangi’s Warden product is one such CSPM tool. Designed to provide continuous monitoring of your Amazon Web Services (AWS) cloud environment to help you identify and detect your top security threats, including cloud misconfigurations. In addition, organizations can use Warden to demonstrate compliance with some of the most common compliance standards and frameworks including PCI DSS, NIST, and GDPR.