Ransomware attacks on the consumer front may have decreased, but on the business end, they have grown 363% year-on-year. There’s no surprise here — if uncurtailed, ransomware can quickly infect and lock a fleet of devices, effectively crippling business operations. The more an attacker can handicap the organization, the more likely the attacker gets paid off.
With the 2018 U.S. ransomwareransomware losses exceeding $3.6 million according to the FBI, organizations can do their part to thwart ransomware attackers, becoming less of a target. After all, there is no guarantee that attackers will return the files back to the organization even after the ransom is paid.
Already, there are helpful resources such as ID Ransomware and No More Ransom to help affected organizations understand the type of ransomware they face, how it works, how it can be removed, as well as to provide technical expertise.
Ransomware is generally classified into three categories — Scareware, Screen Locking Ransomware, and File-Encrypting Ransomware.
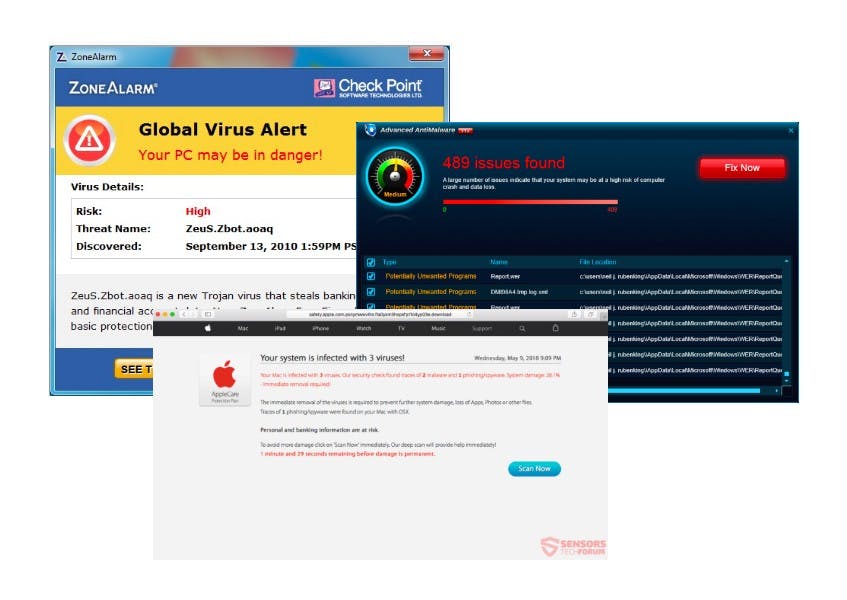
Scareware
Scareware is malware that tricks the user into thinking their computer and files are locked or infected with a virus. The usual demands that follow consist of the user installing a particular antivirus software to delete the virus. While modern browsers and basic security policies now typically block such malware, it pays to know that such scareware can be easily uninstalled by using Task Manager, or simply restarting the computer.
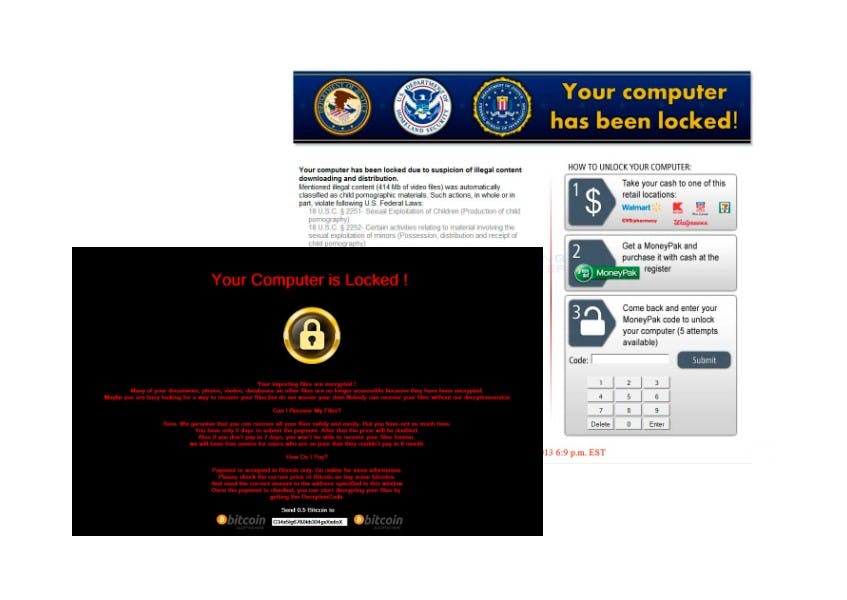
Screen Locking Ransomware
Screen locking ransomware blocks the user from accessing their operating system in any way. By holding the operating system hostage, the organization is forced to do one of these things:
1. Pay the ransom
While it can make sense cost-wise to pay the ransom, we at Horangi never recommend that you pay it. Paying the ransomware demand makes your organization a repeat target, and communicates to other attackers in the know to attack you again.
2. Do a system restore
If the option is available, this is a viable way to remove the ransomware while restoring access to the operating system, but not without potential damage.
3. Attempt to remove the ransomware using third party software
If the organization is able to identify the type of ransomware, it might be able to find legitimate ransomware decryption tools to remove the ransomware. Ransomware Decryptor Site by Kaspersky is one such tool.
However, proceed with caution during your search — many ransomware variants use enterprise-grade encryption that is impossible to crack. Also, some of these tools are actually scareware in disguise that promise fast decryption, only to install more malware.
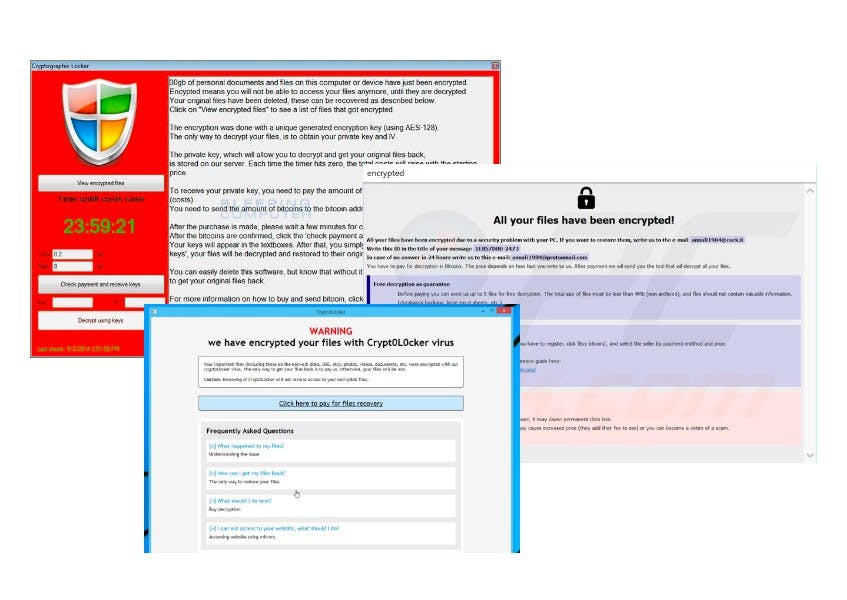
File-Encrypting Ransomware
The most feared form of ransomware is the type that encrypts your business-critical files. NotPetya and WannaCry are prominent examples of this ransomware type. Just this week, Travelex had its customer data held hostage by ransomware attackers who are demanding $6 million for the encryption key. This situation is even affecting Lloyds, Barclays and Royal Bank of Scotland.
When the data encrypted by the attacker is integral to the entire operations of an organization, the organization is essentially in a Catch-22 — paying the ransom is costly and offers no guarantee for resolution of the predicament, yet not paying also gives the public impression that the organization is failing to act.
Stay Ahead of Ransomware Attackers
If an organization does get hit by ransomware, there are comprehensive guides available as to what the organization must immediately do. Isolating the incident and affected endpoints to prevent further infection, for instance, as well as to engage a professional incident response team for investigation. It is even possible to avoid paying the ransom, if malware analysis on the ransomware uncovers methods to decrypt the data, such as finding hardcoded encryption keys.
Obviously, prevention is always preferred. Security professionals should be aware of the common cyber threatscommon cyber threats and web vulnerabilitiesweb vulnerabilities and prior to getting hit, they should take on a risk-based, proactive approach to cybersecurity. This means regularly backing up critical files, operating systems, and possibly keeping the extremely sensitive files offline and out of sight from any attacker.
Having a plan that is disseminated and adhered to across the organization is a proven way to nullify the impact of ransomware attacks. To formulate a practical plan, it makes sense for organizations to do routine cybersecurity assessmentscybersecurity assessments to stay ahead of the cyber threat landscape.