We are thrilled to announce Horangi’s recent mention in Gartner’s report on Emerging Technologies & Trends Impact on Products and Services July 2022 as a sample vendor for Cloud Infrastructure Entitlement Management (CIEM). This is the third consecutive mention of Horangi’s flagship product Warden in Gartner’s security reports. So far, Warden has been listed in Gartner’s Market Guide for Compliance Automation Tools in DevOps with two consecutive mentions as a sample vendor for CIEM.
We believe Horangi being listed as a Sample Vendor in this emerging technologies impact report, especially in the CIEM space, is a testament to the excellence that we strive to deliver. Our flagship product, Warden, is enriched with CIEM, CSPM, Compliance Automation, and Real-Time Threat Detection capabilities. It is a human-centric, agentless security platform that sets up in minutes and delivers only relevant security alerts at the right time, giving your organization the freedom to innovate in the cloud, at build time!
According to the report, “Managing entitlements in cloud infrastructure is a complex task due to rapid growth in their number along with their dynamic and granular nature, but the problem is further aggravated in multicloud environments where the entitlements are inconsistently defined. Cloud infrastructure entitlement management (CIEM) tools help organizations manage cloud access risks via administration-time controls for the governance of entitlements in hybrid and multicloud infrastructure.”
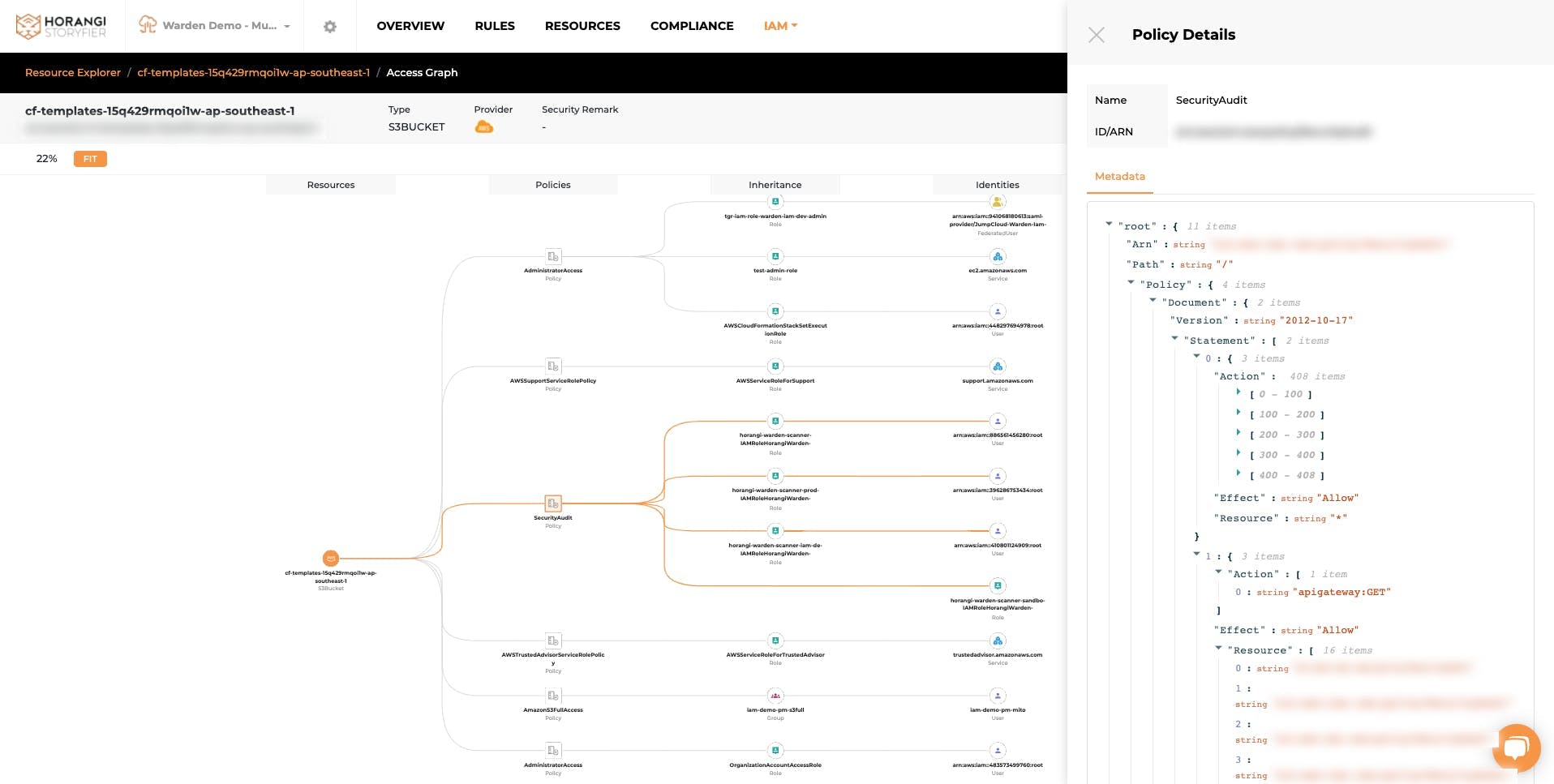
Gartner also highlighted graphical visualization of access rights and entitlements across multicloud environments as one of the key use cases for CIEM offerings. This allows organizations to get a granular view of entitlements associated with a particular identity. Other use cases also include rightsizing permissions, and anomaly detection in user entitlements leveraging advanced analytics and compliance automation.
Graphical Visualization in Warden
At Horangi, we understand that a CIEM tool like Warden fills a gap that exists in traditional IAM tools and CSPM platforms. You can read the full security report on Emerging Technologies & Trends Impact on Product and Services here. (Gartner subscription required)
It is often said that attackers think in graphs and defenders think in lists. The true power of graphs resides not only in displaying information but in helping us frame how we think about relationships between entities and helping us see where we should take action to address issues. Warden’s graphical view can help you gain instant clarity on the excessive permissions and their potential impact on all the resources in your organization. This enables you to save time, and minimize headaches. It makes it easy to resolve excessive permissions, even if your team doesn’t have deep security knowledge. You can just simply copy and paste the proposed policies which are recommended intelligently based on the analysis of historical data. The cherry on top here is that you can also easily preview the potential impact in a graphical format before the update.
Access Path Visualization in Warden IAM
If you are having trouble answering “who has access to my crown jewels and how did they get the access?” then get in touch with us for a quick demo of Warden, a comprehensive cloud security tool with IAM, Threat Detection, and Posture Management capabilities.
Gartner does not endorse any vendor, product, or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.